Computers, Materials & Continua is a peer-reviewed Open Access journal that publishes all types of academic papers in the areas of computer networks, artificial intelligence, big data, software engineering, multimedia, cyber security, internet of things, materials genome, integrated materials science, and data analysis, modeling, designing and manufacturing of modern functional and multifunctional materials. This journal is published monthly by Tech Science Press.
SCI: 2024 Impact Factor 1.7; Scopus CiteScore (Impact per Publication 2024): 6.1; SNIP (Source Normalized Impact per Paper 2024): 0.675; Ei Compendex; Cambridge Scientific Abstracts; INSPEC Databases; Science Navigator; EBSCOhost; ProQuest Central; Zentralblatt für Mathematik; Portico, etc.
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078546 - 08 May 2026
(This article belongs to the Special Issue: Advances in Machine Learning and Artificial Intelligence for Intrusion Detection Systems)
Abstract With the rapid expansion of networked systems, Distributed Denial-of-Service (DDoS) attacks have become a major threat to Internet security and service availability. Due to their limited scalability, incapacity to capture temporal and relational relationships, and decreased detection accuracy under dynamic and high-volume network traffic, traditional machine learning algorithms frequently fail in large-scale DDoS scenarios. This encourages the application of deep learning techniques that can simulate intricate relationships. This survey systematically reviews graph-based deep learning and Transformer models for DDoS detection. We categorize methods for transforming network traffic into graph representations and analyze key architectures, including… More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080050 - 08 May 2026
Abstract Unmanned Aerial Vehicle (UAV) target tracking is one of the key technologies in aerial intelligent perception systems, playing a vital role in applications such as traffic monitoring, border patrol, disaster response, search and rescue, environmental monitoring, and military reconnaissance. Compared with generic object tracking tasks, UAV platforms exhibit significant differences in imaging perspectives, target scales, motion patterns, and onboard computing capabilities, which pose unique challenges for UAV target tracking, including small targets and drastic scale variations, platform motion and motion blur, complex backgrounds and frequent occlusions, low-light conditions at night, as well as real-time and… More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079504 - 08 May 2026
Abstract Large language models (LLMs) are increasingly integrated into recommender systems to support semantic reasoning, natural language understanding, and user-adaptive personalization. However, their reliance on static parametric knowledge and fixed representations limits robustness in dynamic environments, particularly under long-tail and cold-start conditions. Retrieval-augmented architectures have emerged to address these limitations by grounding LLMs in external, non-parametric knowledge sources. This systematic literature review synthesizes 138 peer-reviewed studies published between 2023 and 2025 in conferences and journals, focusing on retrieval-augmented and LLM-enhanced recommendation. We analyze these works through a three-dimensional framework covering: (i) domain application, (ii) semantic feature… More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077625 - 08 May 2026
Abstract Today, technological progress is broad and deep. The next generation networks and systems will integrate features, technologies, and models requiring smooth cooperation between new and old technologies. This survey’s uniqueness is that it considers an integrated, hybrid and heterogeneous future where Internet of Things (IoT), Sixth-Generation (6G) mobile communications technology, and Artificial Intelligence (AI) will work together, providing a smart and connected Intelligent Transportation System (ITS). This smart ITS will give better road safety and optimized travel. Currently, there is a scarcity of surveys focusing particularly on smart ITS that is expected soon. In this More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.074678 - 08 May 2026
Abstract Non-terrestrial networks (NTNs), encompassing unmanned aerial vehicles (UAVs), low-/high-altitude platforms (LAPs/HAPs), and satellite systems, are increasingly enabling Internet of Things (IoT) applications beyond the limits of terrestrial infrastructure. By combining UAV mobility with satellite and HAP coverage, NTN-assisted IoT supports diverse use cases, including remote sensing, smart cities, intelligent transportation, and emergency response. This paper presents a systematic mapping of machine learning (ML) research in NTN-assisted IoT with a focus on security-related aspects. A keyword co-occurrence analysis of over 2000 publications identifies twelve thematic clusters, including three clusters directly related to security, privacy, and trust.… More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077820 - 08 May 2026
Abstract Large language models (LLMs) and related foundation-model workflows are emerging as promising tools for advancing foundry intelligence across the casting value chain. This review examines their applications in material design and property prediction, process parameter optimization and intelligent control, and defect detection and quality tracing in casting environments. The surveyed studies indicate that LLM-enabled systems can help integrate unstructured technical knowledge with multimodal industrial data. This integration supports composition design, simulation-assisted process optimization, diagnostic reasoning, and knowledge-grounded decision support. However, current evidence shows that the transition from pilot demonstrations to robust industrial deployment remains constrained More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077838 - 08 May 2026
(This article belongs to the Special Issue: Development and Application of Deep Learning based Object Detection)
Abstract Steel manufacturing requires high-throughput and high-reliability surface inspection to minimize safety risks, scrap rates, and downstream quality reductions. Conventional rule-based vision and manual inspection are often impeded in real production environments by variable illumination, complex textures, subtle defect morphology, and stringent latency constraints imposed by production-line operation. Deep learning (DL) has become a dominant paradigm for the detection and classification of defects when inspecting steel, but many previous studies have performed broad architectural overviews without explicitly connecting model and pipeline choices to deployment-critical factors such as processing speed, hardware availability, annotation cost, and robustness during… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079131 - 08 May 2026
Abstract Structural optimization is a fundamental step in density functional theory (DFT) calculations, typically driven by the Broyden–Fletcher–Goldfarb–Shanno (BFGS) optimizer. However, the standard BFGS algorithm relies on a local quadratic approximation of the potential energy surface (PES), which frequently breaks down in highly non-quadratic regimes typical of complex surface adsorption systems and defective bulk materials. This breakdown leads to “Hessian pollution”, a phenomenon where higher-order anharmonicities introduce spurious off-diagonal inter-atomic couplings that distort curvature estimates and significantly stall convergence. Herein, we propose a physics-inspired algorithmic intervention to the BFGS method that systematically suppresses this pollution. Once… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076098 - 08 May 2026
(This article belongs to the Special Issue: Advancements in Pattern Recognition through Machine Learning: Bridging Innovation and Application)
Abstract U-Net, a fully convolutional neural network (FCNN) with U-shaped features, has demonstrated significant success in biomedical image segmentation. However, the locality of convolution operations in the U-Net limits its ability to learn long-range dependencies. Transformers, originally developed for natural language processing, have recently been adapted for image segmentation because of their global self-attention mechanisms. Inspired by the long-range feature learning capability of transformers, we propose Dense-Transformer (DenT), an architecture designed for volumetric microscopy image segmentation. DenT incorporates transformers as encoders within each convolutional layer to capture global contextual information. Additionally, dense skip connections at multiple More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077556 - 08 May 2026
Abstract Large Vision-Language models (VLMs) such as Contrastive Language-Image Pretraining (CLIP) have transformed open world image recognition. Nevertheless, few-shot classification, particularly in the extremely low-shot regime, requires not only high accuracy but also reliably calibrated uncertainty for decisions with high confidence. Existing training-free CLIP adapters are primarily designed to increase accuracy and efficiency; integrate the zero-shot text logits with the few-shot feature caches, but not definitely model predictive uncertainty and therefore often exhibit considerable miscalibration and weak selective performance. Bayesian adapters move in the direction of probabilistic modeling by placing priors over adapter parameters and employing… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078873 - 08 May 2026
Abstract With the rapid development of the Internet of Things (IoT), the widespread adoption of applications such as smart homes and industrial IoT has raised the demand for secure authentication and key agreement among resource-constrained devices over open communication channels. Traditional authentication protocols often rely on centralized servers for key distribution, which results in high communication overhead and exposes systems to single-point-of-failure risks. Moreover, IoT devices are typically constrained in computational resources and are vulnerable to hardware cloning. These limitations necessitate lightweight yet robust security mechanisms. To address these challenges, we propose a lightweight peer-to-peer authentication More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078931 - 08 May 2026
(This article belongs to the Special Issue: Intelligent Perception, Decision-making and Security Control for Unmanned Systems in Complex Environments)
Abstract Manned-Unmanned Teaming (MUM-T) is an operational system where manned and unmanned systems perform missions through a collaboration interface, expanding beyond defense into civilian domains. The core of MUM-T lies in the organic interaction between manned and unmanned systems. The Collaboration Interface enabling this interaction becomes a primary target for cyber attacks due to its reliance on wireless networks. Compromising the reliability of the collaboration interface goes beyond simple communication failures; it directly leads to mission failure and aircraft safety issues. Therefore, systematic threat analysis and assessment tailored to this specific domain are essential. This study… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079691 - 08 May 2026
Abstract Indoor intrusion detection is essential for various applications, including security systems and smart homes. Recently, WiFi-based detection has gained popularity due to its low cost and non-invasive nature. Current Channel State Information (CSI) based frameworks primarily use deep learning to extract gait signatures; however, their performance depends heavily on extensive labeled datasets. These methods struggle to differentiate between unlabeled and labeled data that exhibit similar features. To address this challenge, we propose a novel Two-level Feature Fusion model for Indoor Intrusion Detection (TFF-IID) utilizing commercial WiFi CSI. The model adopts a two-level structure to learn… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079331 - 08 May 2026
(This article belongs to the Special Issue: Advances in Efficient Vision Transformers: Architectures, Optimization, and Applications)
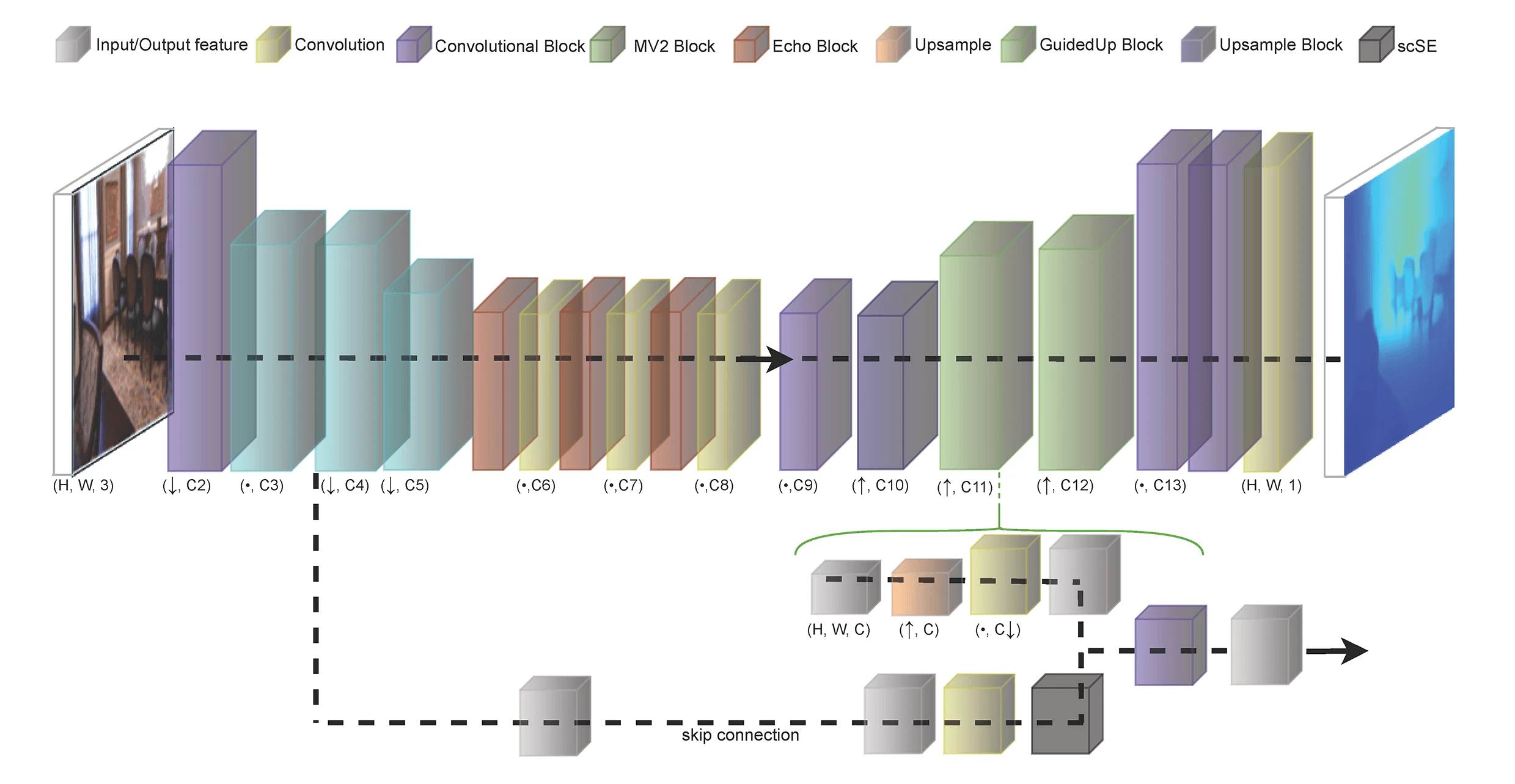
Abstract Monocular depth estimation (MDE) has become a practical alternative to active range sensing in many indoor scenarios, enabled by supervised deep learning models that predict dense depth maps from a single RGB image. However, most modern MDE systems assume mid-to-high resolution inputs and non-trivial compute budgets, limiting their direct applicability in embedded and bandwidth-constrained settings. This paper studies low resolution MDE, focusing on
Graphic Abstract
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079587 - 08 May 2026
(This article belongs to the Special Issue: Advances in Computational Materials Science: Focusing on Atomic-Scale Simulations and AI-Driven Innovations)
Abstract With the rapid development of artificial intelligence and data-driven modeling, deep learning has become an effective tool for analyzing scientific discovery such as predicting material behaviors. Graphene-reinforced copper-based composites, which exhibit excellent mechanical, electrical, and thermal properties, have attracted extensive attention in advanced engineering applications; however, accurate prediction of their stress–strain behavior still relies heavily on computationally expensive molecular dynamics simulations or experiments. In this work, we propose a Graph-based Spatio-Temporal Attention Network, termed GraphSTAN, for stress–strain behavior prediction of copper-based composites. Specifically, atomic-scale initial microstructures are encoded as graphs and integrated with static physical More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077724 - 08 May 2026
Abstract The compression effects on the thermoelastic and thermodynamic properties of cubic zincblende silicon–tin alloy (SiSn) were explored using a multi-methodological approach, deploying data mining methods, theoretical equation-of-state parameters, and the Quasi-Harmonic Debye Model. We analyze the relative volume, isothermal bulk modulus, thermal expansion coefficient, Debye temperature, sound velocity, and microhardness of the SiSn compound under pressures up to 8 GPa. The study commences with the data mining-based searches for a structural model and continues with an analysis of the pressure dependence of the relative volume using the Vinet equation of state, followed by an investigation… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078734 - 08 May 2026
(This article belongs to the Special Issue: Mechanical Behavior of Materials with Advanced Modeling and Characterization)
Abstract Tungsten plays a critical role in semiconductor electrical interconnects, and a thorough understanding of its mechanical properties is essential for optimizing its processing and performance. However, few studies have explored the effect of grain refinement on the mechanical behavior of tungsten. The work indicates a phenomenological transition around ~7.3 nm within the tested grain-size range that governs the nanoindentation response of tungsten. To establish this, we performed molecular dynamics (MD) simulations of nanoindentation for different grain sizes and analyzed surface pile-up, elastic recovery, atomic displacement, loading force, hardness, stress/strain behavior, dislocation density, and dislocation evolution. More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079732 - 08 May 2026
(This article belongs to the Special Issue: Machine Learning in the Mechanics of Materials and Structures)
Abstract The plastic strain accumulation results of the multi-layered wrapped pressure vessel liner during long-term service are an important basis for its safety performance evaluation. However, the complex welds distributed on the liner bring challenges to the calculation of plastic cumulative strain. To this end, a novel hybrid deep learning framework is proposed for the efficient and precise prediction of ratcheting behavior in the liner welds of multilayered pressure vessels. By employing a BiLSTM network to extract bidirectional temporal dependencies from the strain history and incorporating a Multi-Head Attention (MHA) mechanism for adaptive feature weighting, the… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076869 - 08 May 2026
Abstract Blockchain networks are under mounting pressure from emerging complex zero-day attacks that cannot be prevented with conventional security measures. In this paper, we introduce NeuroChain Sentinel, a new bio-inspired cybersecurity model based on spiking neural networks for detecting anomalies in a distributed ledger system in real time. The main innovations are: a Temporal Spike Pattern Recognition algorithm for simulating the biological timing of the neural system to detect malicious transaction patterns; a distributed consensus-verification topology combined with blockchain algorithms; and small-scale neuromorphic engineering, resulting in an 87% reduction in computational load over conventional deep neural… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079708 - 08 May 2026
(This article belongs to the Special Issue: Artificial Intelligence in Visual and Audio Signal Processing)
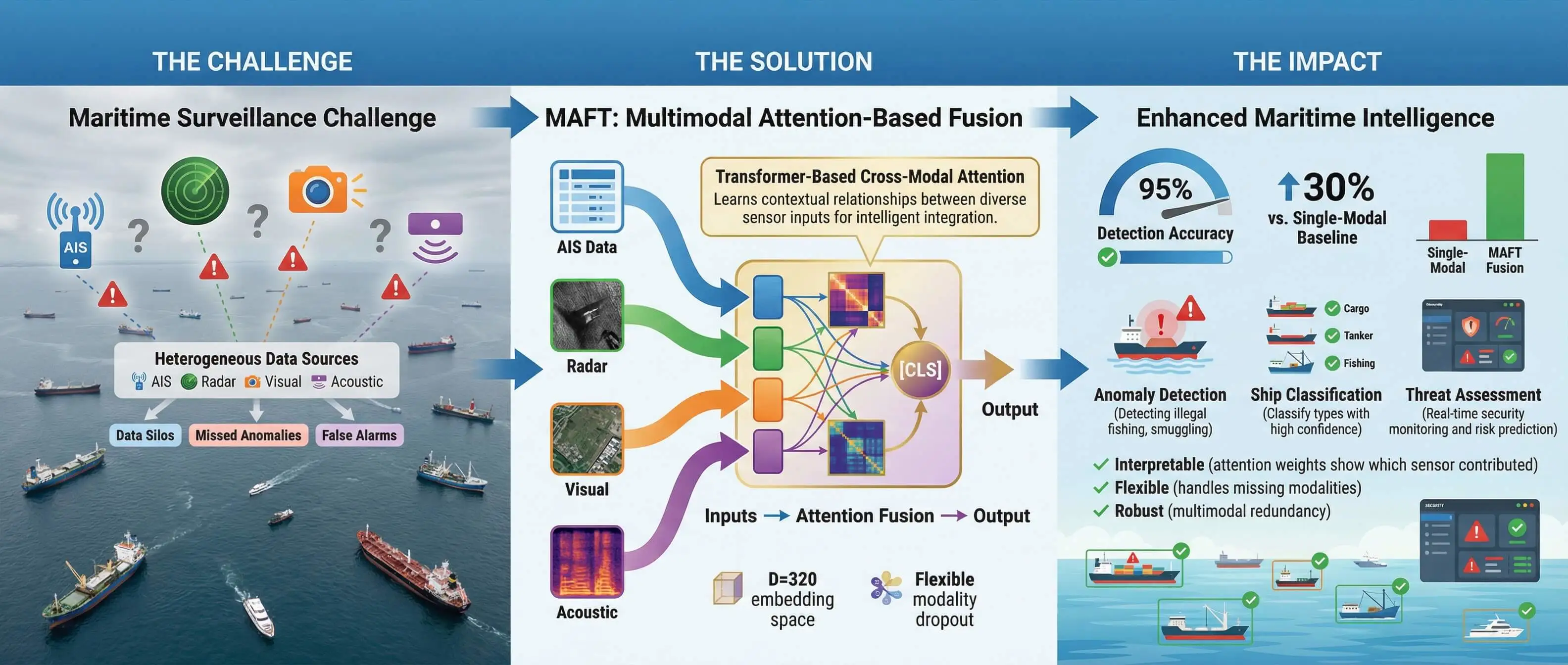
Abstract Maritime Domain Awareness (MDA) is critical for global security and economic stability, yet it is increasingly challenged by sophisticated adversarial tactics such as signal spoofing and “dark vessel” activities. Traditional surveillance systems, often reliant on single-sensor modalities, are ill-equipped to handle these deceptive behaviors. To address this, we propose the Multimodal Attention-based Fusion Transformer (MAFT), a novel deep learning architecture that integrates four distinct data modalities—Aerial imagery, Synthetic Aperture Radar (SAR), acoustic signatures, and Automatic Identification System (AIS) data—to achieve robust and interpretable maritime anomaly detection. A key contribution of our work is a principled… More >
Graphic Abstract
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078105 - 08 May 2026
(This article belongs to the Special Issue: Advances in Wireless Sensor Networks: Security, Efficiency, and Intelligence)
Abstract The rapid proliferation of latency-sensitive applications, coupled with the limitations of service range, has driven the integration of aerial simultaneously transmitting and reflecting reconfigurable intelligent surfaces (ASTAR-RIS) and task offloading to enhance both communication and computational efficiency in wireless sensor networks (WSNs). However, in WSNs, conventional ASTAR-RIS-assisted task offloading faces critical limitations, including restricted endurance, underutilized network caching and computing resources, and inefficient resource allocation within the optimization framework. To overcome these challenges, this paper integrates wireless power transfer (WPT) technology and proposes a novel energy-efficient ASTAR-RIS and WPT-assisted task offloading and content caching framework… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079018 - 08 May 2026
(This article belongs to the Special Issue: Security and Privacy in IoT: Cross-Domain Approaches and Cryptographic Innovations)
Abstract In today’s digitally connected world, where cyber threats are becoming increasingly complex, finding modern and secure text encryption solutions that maintain maximum runtime performance while offering high-level protection is more crucial. The deployment of sophisticated security paradigms is often accompanied by a significant escalation in computational overhead. Thus, the fundamental objective resides in the mitigation of computational overhead while maintaining an uncompromising security posture. Internet of Things (IoT) devices require strong security measures for data transmission. Also, protecting communication channels against illegal access and eavesdropping has become crucial due to the exponential expansion of the… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078756 - 08 May 2026
Abstract Reliable vehicle detection in urban traffic environments remains challenging, particularly for fixed-view CCTV systems deployed in Southeast Asian cities, where heterogeneous traffic composition, high traffic density, frequent occlusions, and complex visual conditions are prevalent. The absence of large-scale datasets tailored to such mixed-traffic environments poses a significant limitation to the performance and generalization capability of existing object detection models. To address this gap, this paper presents a large-scale traffic image dataset for real-time vehicle detection in Vietnamese urban environments. The proposed dataset comprises 23,364 images collected from fixed-view CCTV traffic cameras deployed across Da Nang… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079484 - 08 May 2026
(This article belongs to the Special Issue: Cyberspace Mapping and Anti-Mapping Techniques)
Abstract With the widespread adoption of web applications and cloud services, the OAuth 2.0-based OpenID Connect (OIDC) Single Sign-on (SSO) protocol has become the core of modern digital identity authentication. Although the OIDC protocol itself has strict security specifications, its implementation in real-world web frameworks can introduce critical vulnerabilities, particularly the improper omission of the state parameter, which leads to severe authentication forgery risks. Existing research often overlooks these implementation-level flaws, especially from a formal analysis perspective. This paper addresses this gap by formally analyzing the authentication forgery attack resulting from the missing state parameter. We construct… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078464 - 08 May 2026
Abstract Persistent Infrequent Flows (PIFs) refer to the packet flows that last for a long time but always at low frequencies in network traffic. Accurate identification of the PIFs plays a vital role in intrusion detection, attack prevention, traffic engineering, and other network fields. However, existing methods often require to save all flows for finding out the PIFs due to their infrequency feature, which brings about the problem of low identification accuracy and high memory overhead. To solve this problem, this paper proposes an accurate PIF identification method with low overhead called PIF-Identifier, composed of a… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078634 - 08 May 2026
(This article belongs to the Special Issue: Advances in Cybersecurity for Digital Ecosystems)
Abstract The proliferation of Internet of Things (IoT) devices in the infrastructure of smart cities has posed cybersecurity risks like never before, which have direct implications on the sustainability and energy consumption of cities. In this paper, a multi-faceted Threat-Resilient Energy-Conscious Security Framework (TRECSF) is introduced that combines intrusion detection methods powered by deep learning, blockchain-driven data integrity verification mechanism, and energy-aware security protocols in smart city ecosystems to achieve their sustainability. The new Hybrid Convolutional Neural Network-Long Short-Term Memory (CNN-LSTM) model is introduced to the proposed architecture, which fulfills the purpose of the study to… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079644 - 08 May 2026
(This article belongs to the Special Issue: Attention Mechanism-based Complex System Pattern Intelligent Recognition and Accurate Prediction)
Abstract As 6G-enabled Industrial Internet of Things (IIoT) evolves, green and sustainable industrial monitoring increasingly relies on edge AI to deliver low-latency diagnosis under tight resource constraints. Industrial cyber–physical systems increasingly rely on heterogeneous sensing and communication infrastructures, where network-side attacks can propagate into physical processes and appear as coupled anomalies. Reliable diagnosis therefore requires joint learning from time-synchronized cyber and physical telemetry rather than modeling them as independent signals. This paper develops Cyber–Physical Symbiosis Network (CPSNet), a model designed for edge-AI deployment with a dual-stream architecture for fixed-window multiclass cross-domain anomaly diagnosis in IIoT. CPSNet… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077454 - 08 May 2026
Abstract This study proposes an intelligent Intrusion Detection and Prevention System (IDPS) integrated into a centralized Ryu Software-Defined Networking (SDN) controller to mitigate replay attacks within Internet of Things (IoT) environments. To address the scarcity of specialized datasets, a comprehensive dataset was generated using a real-time SDN-IoT testbed encompassing Mininet, multiple OpenFlow 1.3 switches, and a single Ryu controller. The experimental setup featured the exchange of legitimate and malicious Message Queuing Telemetry Transport (MQTT) traffic between hosts and IoT devices to simulate realistic network behaviors and attack vectors. Our methodology introduces a novel feature engineering framework… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078078 - 08 May 2026
(This article belongs to the Special Issue: Advances in Secure Computing: Post-Quantum Security, Multimedia Encryption, and Intelligent Threat Defence)
Abstract The rapid growth in the field of data and cloud computing has made it essential to ensure information security. Encryption consists of multiple layers, among which a critical component is the Substitution box (S-box). The S-box provides nonlinearity and confusion between the original and cipher forms, and its performance directly determines the security of the cipher against cryptanalysis. Chaotic systems have been widely used for image encryption, however, they suffer from well known limitations such as deterministic periodicity and reduced unpredictability in finite field digital environments. To address these issues, we propose a new S-box… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.075573 - 08 May 2026
Abstract Quantum key distribution (QKD) provides unconditional security but relies on repeaters to extend coverage, thereby introducing repeater trust risks—compromised repeaters may leak keys. Brakerski/Fan-Vercauteren scheme (BFV)-based QKD addresses this issue through key encryption and quantum attack resistance. However, Fast Fully Homomorphic Encryption over the Torus (TFHE) outperforms BFV in encryption/decryption speed for single-qubit homomorphic XOR operations, which is critical for the real-time requirements of QKD. We propose TFHE-based QKD (TQKD), a quantum key distribution protocol based on public-key TFHE. During key forwarding, it leverages the “usable-but-unobservable” property of homomorphic encryption to prevent key exposure. A… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079379 - 08 May 2026
(This article belongs to the Special Issue: AI-Powered Software Engineering)
Abstract Effective pair programming relies heavily on optimal partner compatibility, a requirement that is often difficult to scale manually in software engineering education. This study presents the empirical validation of Codenote, an AI-driven Integrated Development Environment (IDE) designed to automate personality-aware group formation. By integrating a behavioral analysis mechanism, Codenote infers student personality traits from coding patterns to construct complementary pairs, thereby facilitating intelligent collaborative learning. To validate the system’s effectiveness, a controlled experiment was conducted to assess the impact of this AI-mediated pairing strategy on students’ self-efficacy across adaptive, innovative, and persuasive domains. Results indicate… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076717 - 08 May 2026
(This article belongs to the Special Issue: Multimodal Learning for Big Data)
Abstract With the increasing development of ocean information technology, the multi-view fuzzy clustering is attracting increasing attention in pattern mining for massive multi-view ocean data of heterogeneous distributions, owing to its superior performance. However, the previous multi-view fuzzy clustering methods cannot fully consider informative topologies hidden in data distributions, which are crucial to recognize partitions of data. Moreover, they fail to capture invariant structures of multi-view ocean data in learning clustering-specific fusion representation. In addition, they do not take into consideration consistencies contained in the manifolds of data generation in mining soft patterns. To address those… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077977 - 08 May 2026
(This article belongs to the Special Issue: Advances in Image Recognition: Innovations, Applications, and Future Directions)
Abstract Ship re-identification (Re-ID) aims to match ship identities across disjoint camera views and separated time periods, which is critical for maritime target tracking and law enforcement. In real-world surveillance, variations in target distance and viewing angle frequently produce partial views and occlusions, leading to missing geometric components and fragmented appearance cues. Such incomplete observations substantially degrade the robustness and generalization of conventional single-frame methods that rely on global appearance representations. To address these challenges, this study proposes a new ship re-identification framework based on dual-stream feature decoupling and temporal variational Bayesian inference. The proposed method… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076676 - 08 May 2026
(This article belongs to the Special Issue: Privacy-Preserving and Secure Federated Learning for IoT, Cyber-Physical, and Maritime Systems)
Abstract The proliferation of large-scale graph data has enabled Graph Neural Networks (GNNs) to achieve significant success in domains such as recommender systems, social network analysis, and biomedicine. However, in practical networked environments, particularly in distributed service infrastructures, graph data is often isolated between multiple edge smart devices and cannot be shared due to privacy, making GNN models weak in generalization. Subgraph Federated Learning (SFL) mitigates this challenge by treating local client data as subgraphs of the global graph to decentralized GNN training. Unfortunately, client-side missing edges make GNN model difficult to capture dependency information between… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079340 - 08 May 2026
(This article belongs to the Special Issue: Sentiment Analysis for Social Media Data: Lexicon-Based and Large Language Model Approaches)
Abstract This work presents a comprehensive sustainable sentiment analysis system utilizing textual data, designed within a structured client-server architecture for real-time deployment. The system integrates dual feature representations Bag-of-Words (BoW) and Term Frequency–Inverse Document Frequency (TF-IDF) whose prediction scores are combined through a parameter-free score-level fusion strategy. The implementation of the proposed system consists of five major components. The first component involves the acquisition of textual data from various sources, followed by rigorous text preprocessing to eliminate noise and enhance data quality. The second component focuses on feature extraction, ensuring that the extracted features not only… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.075326 - 08 May 2026
(This article belongs to the Special Issue: Advances in Secure Computing: Post-Quantum Security, Multimedia Encryption, and Intelligent Threat Defence)
Abstract Modern intrusion detection systems (IDS) struggle to recognise zero-day cyberattacks, as classical discriminative models rely on historical attack labels and fail to characterise deviations from normal network behaviour. This work presents a hybrid quantum–classical intrusion detection framework in which a Quantum Circuit Born Machine (QCBM) models benign traffic as a probabilistic quantum state. The trained QCBM assigns each network flow a Quantum Anomaly Score (QAS), defined as the negative log-likelihood under the learned benign distribution, which is subsequently fused with classical flow statistics in a Light Gradient Boosted Machine (LightGBM) classifier. The proposed system employs a… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077521 - 08 May 2026
Abstract Multivariate time series anomaly detection (MTSAD) is a critical task for real-time risk control and fault diagnosis in industrial monitoring, aerospace, and financial domains. Unsupervised MTSAD confronts three core challenges: label scarcity in practical scenarios, diverse anomaly patterns that demand adaptive modeling, and weak feature discriminability between normal and anomalous samples. To address these challenges, we propose a Prototype Memory and Contrastive Learning Based Unsupervised Anomaly Detection for Multivariate Time Series method named PC-UAD. PC-UAD comprises three core modules with hierarchical functionalities: (1) A Temporal PatchEmbedder, which adopts learnable positional encoding for dynamic temporal representation… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077803 - 08 May 2026
Abstract With increasing artwork plagiarism incidents, the necessity of using digital watermarking technology for high-quality artwork copyright protection is evident. Current digital watermarking methods are limited in imperceptibility and robustness. To address this, based on comprehensive copyright protection research, we develop a novel watermark framework named ArtFlow, using Invertible Neural Networks (INN). Our framework treats watermark embedding and recovery as inverse image transformations, implemented through forward and reverse processes of INN. To ensure high-quality watermark embedding, we utilize frequency domain transformations and attention mechanisms to guide the watermark into high-frequency areas of the image that have More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078547 - 08 May 2026
(This article belongs to the Special Issue: Intelligent Personalized Recommender Systems: Deep Learning and Multimodal Approaches)
Abstract Aiming at the problems of data sparsity, uneven behavior weight allocation, and insufficient timeliness modeling existing in traditional recommendation systems in the scenario of personalized fashion recommendation, this paper proposes a personalized recommendation method that integrates multi-behavior weights and multi-modal features. A dynamic weighted collaborative filtering algorithm is designed, which comprehensively considers the multi-dimensional behaviors of users, and introduces a time attenuation factor to construct a time-sensitive user-item scoring matrix, so as to more accurately depict the dynamic changes of user interests. A multi-modal deep fusion framework is built: ResNet-50 is used to extract commodity… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077908 - 08 May 2026
(This article belongs to the Special Issue: Multimodal Learning for Big Data)
Abstract Root cause analysis (RCA), which leverages multi-modal observability data (including metrics, traces, and logs) to identify the fundamental source of system failures, is critical for ensuring the reliability of complex microservice systems. Traditionally, RCA has relied on human engineers to manually correlate these fragmented signals, which is a labor-intensive and error-prone process. Although recent AIOps advancements, particularly those leveraging Large Language Models (LLMs), aim to automate this workflow, they remain constrained by limitations. Existing methods often rely on single-modal data, restricting diagnostic comprehensiveness. Furthermore, approaches that utilize multi-modal data typically depend on simplistic temporal alignment,… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079241 - 08 May 2026
(This article belongs to the Special Issue: Next-Generation Cybersecurity: AI, Post-Quantum Cryptography, and Chaotic Innovations)
Abstract Web 4.0 platforms introduce intelligent, decentralized agents and real-time interactions that increase both utility and attack surface. This paper presents a comprehensive, reproducible AI blockchain hybrid designed to (1) detect SQL injection attacks at scale using a textual TFIDF + machine-learning pipeline, (2) incorporate reputation signals from a real-world Bitcoin OTC trust dataset to compute a TrustAlert Score (TAS) that prioritizes alerts and guides logging policy, and (3) record privacy-preserving audit digests on blockchain, optionally attested via a zero-knowledge proof (ZKP) pipeline. We evaluate the system on a 148 k SQL corpus and Soc-SignBitcoinOTC reputation More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078591 - 08 May 2026
Abstract The rapid growth of networked systems and the increasing diversity of cyberattack behaviors have posed significant challenges to intrusion detection, particularly in scenarios characterized by high-dimensional features and severe class imbalance. Conventional detection approaches based on handcrafted rules or shallow representations often exhibit limited robustness under such conditions. To address these issues, this paper presents a hybrid deep learning framework for network intrusion detection that integrates complementary feature learning mechanisms within a dual-branch architecture. Specifically, a Transformer branch is employed to model long-range temporal dependencies in network traffic, while a convolutional neural network branch (CNN)… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077982 - 08 May 2026
(This article belongs to the Special Issue: Sentiment Analysis for Social Media Data: Lexicon-Based and Large Language Model Approaches)
Abstract Multimodal sentiment analysis aims to accurately identify emotional states by comprehensively utilizing information from multiple sources such as text, audio, and visual data. However, semantic heterogeneity and temporal differences exist between different modalities, limiting the effectiveness of feature fusion. To address this issue, this paper proposes a hierarchical joint cross-modal attention and gating mechanism (HJCAG) for multimodal sentiment analysis. This method introduces a hierarchical structure, dividing modal interactions into bimodal and trimodal layers to progressively model the semantic relevance between modalities. First, deep features are extracted from text, audio, and visual modalities using pre-trained models… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078181 - 08 May 2026
(This article belongs to the Special Issue: Advances in Wireless Sensor Networks: Security, Efficiency, and Intelligence)
Abstract For the wide-coverage application scenarios, wireless rechargeable sensor networks are normally divided into multiple clusters to support the diversity and flexibility for monitoring, and use the mobile charger (MC) to support the sustainable charging of the network. Many efforts focus on optimizing the cluster head selection and mobile charger scheduling to improve the network energy efficiency and reliability. However, the existing work tends to use fixed triggering mechanism for cluster head (CH) rotation, and may trigger the rotation either too early or too late. Besides, the existing charging triggering mechanisms cannot track the changes in… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078998 - 08 May 2026
Abstract Mobile Edge Computing (MEC) facilitates the rapid response and energy-efficient execution of tasks on mobile devices. However, determining whether and where to offload tasks remains a significant challenge due to the constantly changing character of workloads in MEC environments. To address this issue, this paper proposes PreAlloc-A2C—a deep reinforcement learning actor-critic-based framework that calculates allocation scores by leveraging both task features (task size, required completion time, and waiting time) and server features (queue length and historical workload). This design enables fully distributed task offloading decisions without centralized coordination. Additionally, a Long Short-Term Memory (LSTM) network More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080112 - 08 May 2026
Abstract Printed circuit boards (PCBs) are essential components that strongly influence the performance and reliability of modern electronic systems. However, minor and visually subtle manufacturing defects can degrade product quality and pose serious challenges for automated inspection systems. Existing deep learning–based methods often struggle to simultaneously achieve high detection accuracy, real-time processing speed, and compact model size. This study proposes an enhanced approach for real-time PCB defect detection using advanced object detection models. A dedicated dataset of bare PCBs was developed and carefully annotated with six defect categories: open circuits, missing holes, spurs, mouse bites, short… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078280 - 08 May 2026
(This article belongs to the Special Issue: Intelligent Perception, Decision-making and Security Control for Unmanned Systems in Complex Environments)
Abstract The development of Unmanned Surface Vehicles (USVs) has become a key focus in marine robotics, fueling the need for navigation systems capable of performing complex and delicate tasks with speed and precision. However, the end-to-end path tracking process often encounters challenges in learning efficiency, and generalization, and varying environmental conditions. To achieve sample-efficient and robust USV navigation in dynamic maritime environments, the paper proposes a novel hierarchical multi-view latent imitation learning (IL) architecture. By formulating a latent IL objective, the framework disentangles diverse navigation modalities through continuous variables, preventing mode collapse and enhancing behavioral adaptability… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.075102 - 08 May 2026
Abstract Federated learning (FL) enables collaborative model training across decentralized clients without sharing raw data, thereby preserving privacy. However, in real-world FL deployments—such as sensor-based activity recognition, wearable health monitoring, and industrial Internet of Things, where local training data often suffer from heterogeneous noisy labels due to diverse collection environments, sensor limitations, and labeling errors. These noisy labels, typically distributed unevenly across clients due to differences in client-side annotation, exacerbate Non-Independent and Identically Distributed (non-IID) data issues, leading to biased updates, unstable convergence, and degraded global model performance. Accurate estimation of client-specific noise rates is therefore… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077928 - 08 May 2026
(This article belongs to the Special Issue: Advances in Intrusion Detection and Prevention Systems)
Abstract Traditional malware detection models rely on a single feature source for detection, resulting in high false positive or false negative rates due to incomplete information. In addition, conventional models depend on manual feature engineering, which is inefficient and hard to adapt to new malware variants. To address these challenges, this paper proposes a malware detection model called WAFDect based on a self-attention mechanism with multi-source feature fusion. The model consists of two key designs. First, we construct a multi-source feature extraction model that analyzes multi-source data such as API call sequences, registry operation logs, file… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079734 - 08 May 2026
Abstract Accurate short-term load forecasting is essential for reliable power system operation, particularly under the increasing uncertainty caused by abnormal weather and socio-economic fluctuations. This study presents a month-conditioned boosting framework that integrates SHapley Additive Explanations (SHAPs) into model refinement. A baseline XGBoost model was first compared with linear and tree-based regressors, followed by enhancements through lagged and rolling-window features as well as loss weighting for vulnerable months. To further improve the performance, SHAP analysis was employed to identify the dominant error-contributing features, which guided the construction of targeted month-specific interaction terms for retraining. Experimental results More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076283 - 08 May 2026
(This article belongs to the Special Issue: Advances in Machine Learning and Artificial Intelligence for Intrusion Detection Systems)
Abstract Traditional Intrusion Detection Systems (IDSs) that rely on fixed signatures or basic machine learning often struggle with sophisticated, multi-stage cyberattacks and previously unknown threats. To fix these problems, this paper introduces IntrusionNet, a mixed deep learning system that combines Convolutional Neural Networks (CNN), Recurrent Neural Networks (RNN), and Autoencoders in a two-part design. Differing from typical stacked models, IntrusionNet works on two levels at the same time. First, a supervised CNN-RNN process pulls spatial-temporal data from traffic flows to sort well-known attack patterns. Second, an unsupervised Autoencoder process spots new anomalies by looking at reconstruction… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078473 - 08 May 2026
Abstract In recent years, the rapid development of artificial intelligence has greatly promoted the application of Machine Learning as a Service (MLaaS). Users can upload their requirements through front-end applications, and the server provides model inference services after receiving the user input. However, MLaaS may lead to serious privacy breaches. Large language model services are typical representatives of MLaaS, and the Transformer is a typical structure in large language models. Therefore, this paper proposes a privacy-protected Transformer inference scheme based on the CKKS fully homomorphic encryption scheme to optimize computational and communication efficiency. Firstly, this paper… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.075960 - 08 May 2026
Abstract Public safety and security remain critical concerns in urban environments. Detecting suspicious activities in densely populated areas poses significant challenges for modern smart cities due to occlusions, limited fixed-camera coverage, and the dynamic nature of large crowds. To address this problem, this paper proposes a Artificial Intelligence (AI)-driven unmanned aerial surveillance framework for proactive monitoring and abnormal activity recognition. The system leverages an Long-term Recurrent Convolutional Network (LRCN)-enabled architecture capable of extracting spatiotemporal patterns from aerial video streams, allowing it to detect suspicious behavior with high precision. Three deep learning models are comparatively evaluated: (i)… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078089 - 08 May 2026
(This article belongs to the Special Issue: Artificial Intelligence in Visual and Audio Signal Processing)
Abstract Visual speech recognition (VSR) aims to infer spoken content from visual observations of articulatory movements. Despite significant progress, it remains a challenging task in computer vision and speech processing. Its difficulty arises from pronounced speaker-to-speaker variability, the presence of homophenes (phonemes that are visually indistinguishable), changes in illumination, and the intrinsically high-dimensional nature of spatiotemporal lip dynamics. In this work, we propose NestLipGNN, a graph-based framework that integrates Graph Neural Networks (GNNs) with a nested multi-granularity learning strategy for visual speech recognition. We construct dynamic lip graphs from facial landmarks to model both spatial relationships… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077994 - 08 May 2026
(This article belongs to the Special Issue: Next-Generation Cybersecurity: AI, Post-Quantum Cryptography, and Chaotic Innovations)
Abstract Quantum Key Distribution (QKD) ensures secure key establishment through the principles of quantum mechanics; however, its effectiveness in practice hinges on dependable identity verification via classical channels during the post-processing phase. Current QKD implementations typically depend on pre-existing symmetric-key authentication, which suffers from limited scalability and complicated key management in extensive networks. Authentication methods utilizing post-quantum cryptography (PQC) signatures, based on complex mathematical assumptions, introduce extra and uncertain security dependencies, potentially compromising the security model integrity that QKD aims to maintain. This paper explores the application of hash-based signatures (HBS) for identity verification in the… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078997 - 08 May 2026
Abstract With the rapid growth of social media and frequent anonymous interactions, hate speech has become widespread. As users express diverse opinions in digital spaces, the need for effective detection remains crucial. To address this, we propose a framework applicable to diverse hate speech types, combining sentence-level semantic representation vectors from the pre-trained Bidirectional Encoder Representations from Transformers (BERT) with sentiment score vectors from the Linguistic Inquiry and Word Count (LIWC) dictionary and the Valence Aware Dictionary for sEntiment Reasoning (VADER). This semantic-sentiment fusion integrates three deep learning models—Convolutional Neural Network (CNN), Long Short-Term Memory (LSTM), More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077782 - 08 May 2026
Abstract Regression testing of large-scale, data-intensive software systems demands efficient test-case prioritization strategies to detect faults early while minimizing computational cost. Conventional prioritization methods, such as coverage-based and risk-based approaches, lack adaptability to evolving project dynamics and fail to leverage the rich test-execution data accumulated over continuous integration cycles. This study presents a Data-Driven Test-Case Prioritization (DD-TCP) Framework that incorporates statistical and machine-learning techniques to model the relationship between test-case features and historical fault detection outcomes. The framework extracts multidimensional attributes including code-change frequency, dependency metrics, execution duration, and past failure density, which are normalized and… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.074115 - 08 May 2026
(This article belongs to the Special Issue: Deep Learning: Emerging Trends, Applications and Research Challenges for Image Recognition)
Abstract Group activity recognition in public environments is challenging due to dynamic formations, complex inter-person interactions, and frequent occlusions. Existing methods often emphasize individual actions, overlooking collective behavioral patterns. This work introduces a multi-modal framework integrating silhouette-based appearance and skeleton-based pose information for robust recognition in surveillance scenarios. You Only Look Once v11 (YOLOv11) detects persons, Segmenting Objects by LOcations version 2 (SOLOv2) segments instances, and AlphaPose extracts skeletons, followed by hierarchical grouping to form spatially coherent clusters. A hybrid feature extraction strategy combines handcrafted descriptors (Extended GIST (ExGIST), Distance Transform, Binary Robust Independent Elementary Features More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078727 - 08 May 2026
Abstract We propose a Gloss-Internal Graph Construction and Encoding framework that represents compound glosses as directed, labeled graphs and integrates them into a Transformer via a graph-aware encoder. We evaluate our approach against Rule-Based Gloss Decomposition (RBGD) and Linear Gloss Sequence Encoding (LGSE) baselines on ASLG-PC12 and PHOENIX-2014T. Results show consistent improvements over both baselines, achieving gains of up to +3.2 BLEU-4 over LGSE and +7.0 BLEU-4 over RBGD on ASLG-PC12. On PHOENIX-2014T, our method yields gains of up to 1.9 BLEU-4 on the development set and 2.4 BLEU-4 on the test set. Ablation studies further More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.075234 - 08 May 2026
(This article belongs to the Special Issue: Advanced Bio-Inspired Optimization Algorithms and Applications)
Abstract This study introduces a hybrid routing protocol, Low Energy Adaptive Clustering Hierarchy—Ant Colony Optimization—Genetic Algorithm (LEACH-ACO-GA), for wireless sensor networks. It combines regional ant colony optimization for cluster head selection with inter-cluster routing based on a genetic algorithm. The proposed method reduces energy consumption from 6.9 J (LEACH Classic) to 5.6 J (LEACH-ACO-GA) and decreases latency from 460 to 390 ms, while maintaining a packet delivery ratio of 0.97. These values are averaged over 70 rounds based on 30 independent simulation runs conducted on networks with 50 and 200 nodes. The hybrid method extends network More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077655 - 08 May 2026
(This article belongs to the Special Issue: Development and Application of Deep Learning based Object Detection)
Abstract Many occluded and ambiguous ground truths exist in object detection, making detectors unable to obtain optimal training samples. In this article, we revisit the suboptimal sample issue in label assignment for object detection and propose a novel detector-agnostic strategy, termed FSS, to address it. FSS reformulates label assignment as the process of selecting high-quality sub-optimal samples and progressively transforming them into optimal ones. Specifically, for each candidate, we estimate the probability of being an optimal sample by jointly considering localization quality and classification confidence, thereby constructing an instance-wise probability matrix. Based on the spatial distribution More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076992 - 08 May 2026
(This article belongs to the Special Issue: Utilizing and Securing Large Language Models for Cybersecurity and Beyond)
Abstract Phishing emails are an increasing threat to both individuals and organizations, demanding more sophisticated methods of detection beyond traditional blacklisting and heuristic techniques. One of the main challenges in phishing detection is the limited availability of high-quality phishing datasets. To address this issue, we use generative AI to create synthetic emails that help reduce class imbalance, improve model generalization, and overcome data scarcity. We employ a large language model, DeepSeek-7B-Chat, to generate realistic and context-aware phishing and non-phishing emails. Through prompt engineering and fine-tuning, the model produces diverse and modern phishing-style emails that strengthen phishing… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.075265 - 08 May 2026
(This article belongs to the Special Issue: Artificial Intelligence Methods and Techniques to Cybersecurity)
Abstract The detection of zero-day malware represents one of the most significant challenges in contemporary cybersecurity. In this paper, we introduce a novel concept called “Negative-One-Day Malware Detection”, which aims to identify potentially malicious software before it is actually created by threat actors. Our approach leverages recent advancements in generative AI, specifically diffusion-based generative models, to generate and analyze potential future malware variants. By doing so, we can train detection systems to recognize these variants before they emerge in the wild, thereby closing the critical protection gap that currently exists between malware creation and detection. We More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079684 - 08 May 2026
(This article belongs to the Special Issue: Advancing Edge-Cloud Systems with Software-Defined Networking and Intelligence-Driven Approaches)
Abstract In the cloud-edge collaborative network, advanced persistent threats (APTs) pose a serious security risk to critical network assets. Although network deception defense can mislead attackers’ cognition, its effectiveness depends on dynamically selecting appropriate rotation timings of the deception defense. However, the deployment of deception resources and state updates is not completed instantaneously, and existing methods ignore the state transition delay and the dynamic interaction between the attackers and defenders during the real attack and defense process. To address this, we propose a deception defense timing selection method based on the time-delayed FlipIt game. Firstly, a… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079991 - 08 May 2026
(This article belongs to the Special Issue: Integrating Computing Technology of Cloud-Fog-Edge Environments and its Application)
Abstract Mobile fog computing must support latency-sensitive applications under dynamic user mobility and time-varying network conditions. Existing mobility-aware scheduling approaches are largely reactive and often ignore prediction uncertainty, resulting in service disruptions and inefficient task migration. This paper proposes an uncertainty-aware digital twin-based orchestration framework for proactive mobility-aware fog computing. The framework maintains real-time synchronized digital twins of users and fog nodes and integrates a hybrid Gated Recurrent Unit-Exponentially Weighted Moving Average (GRU-EWMA) mobility prediction model with fog-load forecasting to enable joint mobility- and load-aware decision-making. An entropy-based confidence mechanism is introduced to regulate proactive handover More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079393 - 08 May 2026
(This article belongs to the Special Issue: Development and Application of Deep Learning based Object Detection)
Abstract With the increasing refinement of ornamental fish culture, understanding fish behavioral patterns has become critical. Fish movements not only reflect daily activity ranges but also reveal responses to environmental changes such as water currents and obstacles. However, traditional manual observation is limited by manpower and time, making it difficult to record fish behaviors over long periods stably. Existing automated tracking techniques often suffer from ID switches and track interruptions caused by rapid fish movement, occlusions, or intermingling, which in turn degrade the reliability of subsequent analyses. This paper proposes a deep learning-based multi-object fish tracking… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079959 - 08 May 2026
Abstract Robots perform diverse tasks in real-world scenarios. In safety-critical applications, robot control must prioritize satisfying safety constraints in addition to achieving high performance. Offline safe reinforcement learning avoids risky online exploration by training from a given dataset. However, most existing methods overlook two issues in offline data. First, non-zero cost signals are typically sparse, which leads to inaccurate cost value estimates and makes it difficult to impose effective safety constraints on the policy. Second, an imbalanced dataset biases policy learning toward unsafe behaviors. To address these challenges, we propose an actor-critic method ARMOR (multi-scAle Reweighting with Multi-task… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078074 - 08 May 2026
(This article belongs to the Special Issue: Deep Learning for Emotion Recognition)
Abstract With the popularization of multimodal content on social media, accurately identifying sarcastic intent is of great significance for understanding public attitudes and grasping public opinion trends. However, sarcastic expressions rely on context, exhibit inconsistencies in multimodal information, and have implicitly contradictory semantics. These characteristics pose challenges to traditional single-text modality methods. Existing multimodal methods, due to their default assumption of symmetric modal interactions and difficulty in capturing the subtlety of sarcasm and modal contradictions, yield limited detection performance. Therefore, this paper proposes a quantum-inspired complex-valued fusion framework to optimize the intra-modal semantics and inter-modal fusion… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076620 - 08 May 2026
(This article belongs to the Special Issue: Artificial Intelligence in Manufacturing and Remanufacturing Systems)
Abstract The increasing complexity of steel manufacturing and the rising demand for customized high-grade plates have intensified the need for efficient and defect-aware cutting optimization. In practical production, mother plates frequently contain multiple surface defects, and the cutting process is further constrained by delay-sensitive operations such as tool-change sequences and defect-tolerance requirements. To address these challenges, this study formulates the Defective Multi-Inventory Mother-Plate Two-Dimensional Cutting Stock Problem (DMMP-2CSP) as a multi-objective model that simultaneously maximizes cutting profit and minimizes tool changes under strict geometric and defect-avoidance constraints. We develop an Improved Multi-Objective Grey Wolf Optimizer (IMOGWO) More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077465 - 08 May 2026
(This article belongs to the Special Issue: Advancements in Deploying Blockchain in the Cloud of Things (CoT))
Abstract The Internet of Things (IoT) devices generate massive data that leads to network congestion, propagation delays, and suboptimal resource allocation. Traditional Cloud Computing (CC) offers scalable resources required for that data; however, it has a long delay and communication overhead. On the other hand, Edge Computing (EC) guarantees low latency but has limited computational capacity. In this paper, we propose an intermediate paradigm, Regional Computing (RC), combined with a Fuzzy Logic System (FLS) for dynamic, multi-criteria offloading across edge, regional, and cloud. The FLS takes task size, cost, and computational demand as input metrics. It More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076994 - 08 May 2026
(This article belongs to the Special Issue: AI-Driven Big Data Analytics for Sustainable Mixed Traffic and Mobility Systems)
Abstract This study presents a novel integrated framework for autonomous vehicle control at unsignalized intersections in mixed traffic environments, addressing the critical challenge of coordinating Society of Automotive Engineers (SAE) level 4 connected and autonomous vehicles (CAVs) and manually driven vehicles (MVs). The combination of driving intention prediction with a Social Long Short-Term Memory (Social LSTM) and a scheduling algorithm with optimization-driven Pass-through Time Windows (PTWs) is adopted to address traffic flow uncertainty. The Social LSTM model with spatial pooling layers to capture complex multi-vehicle interactions and predict surrounding vehicles’ trajectories and maneuver intentions using naturalistic… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078894 - 08 May 2026
Abstract Many sensing and imaging modalities naturally yield complex-valued signals, where magnitude and phase jointly convey information. Complex-valued neural networks (CVNNs) possess unique advantages in processing phase-sensitive data (e.g., synthetic aperture radar (SAR) and magnetic resonance imaging (MRI)), yet their widespread adoption is hindered by significant computational overhead and training instability. To address these challenges, this paper presents the Wirtinger Derivative Complete Complex Network (WCCN), a unified and efficient framework for complex-valued deep learning. The proposed framework systematically addresses three key challenges in CVNNs: computational efficiency, parameter redundancy, and training stability. WCCN integrates three core components.… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077157 - 08 May 2026
Abstract With the increasing connectivity and intelligence of Internet-of-Things (IoT) devices, which interface with numerous aspects of our daily lives, security remains a major concern for IoT devices deployed in e-healthcare systems. The existing solutions demonstrate that authentication of IoT devices across all domains, especially in healthcare, poses significant vulnerabilities, including side-channel, insider, and replay attacks. Alternatively, it is not feasible for resource-constrained IoT devices due to the computational, communicational, and space overheads of modular exponentiation or bilinear pairing, or because it requires four to five round-trips for authentication. The rapid growth of IoT in the… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077057 - 08 May 2026
(This article belongs to the Special Issue: Deep Learning for Emotion Recognition)
Abstract Human emotions are intricate and difficult to decipher through various modalities. Current methodologies frequently employ inflexible fusion strategies that do not consider the dynamic and context-sensitive characteristics of emotional expressions in both visual and textual mediums. This paper presents SYMPHONIA (Synchronizing Facial and Textual Modalities for Emotion Understanding), an innovative architecture engineered to capture and amalgamate emotional signals from facial expressions and language, attuned to contextual and modality interactions. There are two parts to SYMPHONIA: a Facial Emotion Branch that uses Vision Transformers and facial landmarks, and a Textual Emotion Branch that uses RoBERTa embeddings… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.074282 - 08 May 2026
Abstract The rapid growth of the Internet of Things (IoT) has led to dense wireless sensor networks (WSNs) deployed in critical applications such as smart cities, industrial monitoring, and healthcare. However, energy constraints, unpredictable communication delays, and inefficient data aggregation remain significant challenges that limit network reliability and operational lifespan. Traditional approaches often fail to balance delay minimization with energy efficiency, especially in large-scale or dynamic networks. To address these issues, this study proposes CTSO-DRNN, a novel framework that integrates Chronological Tangent Search Optimization (CTSO) with a Deep Recurrent Neural Network (DRNN) for accurate delay prediction… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079701 - 08 May 2026
Abstract Malware remains a persistent and evolving threat to digital security, highlighting the need for advanced and resilient detection frameworks capable of mitigating increasingly sophisticated and evasive cyberattacks. Although deep learning ensembles have been explored, many existing approaches fail to balance computational efficiency with the diverse feature extraction capabilities needed for complex variants. To address this gap, this study proposes a novel stacking ensemble framework, MalDetect-IoT, which specifically eliminates the requirement for manual feature engineering and domain specific preprocessing traditionally required in malware classification. By fine-tuning two pre-trained models MobileNetV3 for its lightweight efficiency and Xception… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078416 - 08 May 2026
(This article belongs to the Special Issue: Advancements in Pattern Recognition through Machine Learning: Bridging Innovation and Application)
Abstract Unmanned Aerial Vehicle (UAV) image object detection has been widely applied in many fields. However, compared with ordinary natural images, UAV images often exhibit complex backgrounds, a predominance of small objects, and significant variations in target scales, which cause traditional detection algorithms to easily suffer from missed or false detections with insufficient accuracy. To address these issues, this paper proposes a novel UAV image object detection algorithm named DMA-YOLO based on the YOLOv8s model, incorporating a deep diverse branch block and multi-scale auxiliary feature. First, a DF-C2f module integrating a deep diverse branch block and… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080737 - 08 May 2026
Abstract Refactoring improves maintainability without altering externally observable behavior, yet it remains costly and error-prone when applied manually at scale. While large language models (LLMs) can generate plausible refactorings, practical adoption is limited by uncontrolled edit scope, inconsistent outputs under stochastic decoding, and weak traceability of why a change was produced. This paper proposes a smell-targeted, scope-bound refactoring framework for JavaScript that couples deterministic AST-based smell detection with constrained LLM transformation. The key design principle is to bind generation to explicitly detected smell instances, enforce a structured output contract (refactored code plus per-smell rationale), and log… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080632 - 08 May 2026
(This article belongs to the Special Issue: Malware Analysis, Forensics, and Detection Using Artificial Intelligence)
Abstract Accurate malware identification and family categorization remain significant challenges in large-scale Android software analysis. Although deep learning has surpassed traditional machine learning in performance, its widespread adoption is hindered by the computational overhead stemming from feature redundancy and the lack of interpretability inherent in its black-box nature. To address these issues, this paper proposes DroidNTA, a DL-based detection model that fuses network traffic and API features. The model first constructs a simplified API Call Graph by extracting the intrinsic structural attributes of applications, and subsequently generates API feature vectors from invocation sequences using a Markov More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079214 - 08 May 2026
Abstract This paper investigates the joint resource allocation problem in Reconfigurable Intelligent Surface (RIS)-assisted cooperative non-orthogonal multiple access device-to-device (CNOMA-D2D) cellular networks. To tackle the high-dimensional non-convex joint optimization of power control, RIS phase configuration and channel assignment, we propose an integrated user pairing strategy, PIP-UP, quantifying utility through factors, phase alignment, interference suppression and power difference, neglected in existing methods. Furthermore, we develop a hybrid deep reinforcement learning algorithm, A3TD, combining the parallel exploration capability of Asynchronous Advantage Actor-Critic (A3C) with the stable continuous optimization of Twin Delayed Deep Deterministic Policy Gradient (TD3). This integration More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.076553 - 08 May 2026
(This article belongs to the Special Issue: Advanced Localization and Multi-Sensor Fusion in WSN, IoT & VANET)
Abstract The Internet of Things (IoT) enables seamless real-time monitoring and data exchange across distributed and heterogeneous environments with wireless sensor networks (WSNs). The open architecture and resource constraints of wireless sensor networks (WSNs) make them highly vulnerable to internal security threats caused by malicious or compromised nodes, particularly in Internet of Things (IoT) environments. To address this issue, we proposed Dynamic Trust Evaluation Model (DTEM), designed to provide a secure, scalable, and efficient framework for IoT-based WSNs. The proposed model identifies the role of trust management in routing, data aggregation, and intrusion detection, including trust-based… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079440 - 08 May 2026
(This article belongs to the Special Issue: Development and Application of Deep Learning and Image Processing)
Abstract Healthcare, education, technological advancement, and farming are the key challenges facing developing countries, with agriculture unquestionably playing an important role in economic growth. Ensuring adequate food production is essential for citizens’ survival, as it is anticipated that efforts in this area would result in increased food productivity. A key approach to enhancing field productivity involves meticulous care of its components, starting with the production of crops. Wheat leaf rust poses a severe threat, particularly to young seedlings, constituting a significant fungal disease that can cause a 25% reduction in wheat productivity. To overcome these issues,… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080490 - 08 May 2026
Abstract The integration of Internet of Things (IoT) infrastructures with Distributed Ledger Technologies (DLT) remains challenging due to the reliance on complex, tightly coupled back-end systems or centralized oracle services that hinder scalability, maintainability, and trust. This paper introduces a lightweight middleware architecture based on a Low-Code Development Platform (LCDP) that enables flexible and secure IoT-to-blockchain orchestration. We develop a custom workflow extension for the n8n platform that supports direct interaction with smart contracts, thereby removing the need for third-party oracle intermediaries. The proposed system was evaluated in a real-world deployment involving a network of Netatmo More >
 Open Access
Open Access
RETRACTION
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.083417 - 08 May 2026
Abstract This article has no abstract. More >
 Open Access
Open Access
RETRACTION
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.083414 - 08 May 2026
Abstract This article has no abstract. More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079917 - 08 May 2026
(This article belongs to the Special Issue: Advancements in Evolutionary Optimization Approaches: Theory and Applications)
Abstract To ensure an effective disturbance response and maintain continuous production in hybrid flow shops, this paper focuses on the design of a rescheduling method. A rescheduling model is constructed that minimizes the makespan, total tardiness, and scheme deviation degree. A hybrid rescheduling driving mechanism based on the latest completion time is designed to effectively trigger rescheduling. The Whale Optimization Algorithm (WOA) is improved by integrating the good point set theory, nonlinear control parameter strategy, and Differential Evolution (DE) algorithm. Moreover, non-dominated sorting and a dynamic external archive mechanism based on crowding distance are introduced to More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080068 - 08 May 2026
(This article belongs to the Special Issue: Advanced Edge Computing and Artificial Intelligence in Smart Environment)
Abstract The deployment of specialized language models in resource-constrained edge environments (
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079584 - 08 May 2026
Abstract Intelligent Transportation System (ITS) interconnects smart technologies for the advancement in communication and autonomous decision making in vehicle interactions. It manages traffic control infrastructure, analyses road conditions, and supports cooperative awareness in a crucial environment. The sensors continuously collect real-time vehicle data, process it, and forward it to analysis servers to predict the behavior of Vehicular Ad hoc Networks (VANETs). Many approaches have been proposed to address research challenges in routing and improve communication for vehicle-to-vehicle (V2V) and vehicle-to-infrastructure (V2I) systems. However, due to dynamic topology, the network becomes disturbed and loses established connections, leading… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077916 - 08 May 2026
Abstract Manipulating objects based on verbal commands in cluttered environments remains a critical challenge in robotic arm research. Verbal commands possess high semantic abstraction, while precise grasping and placement actions rely on fine-grained geometric perception. The disparity between these two domains is the primary cause of operational errors. Particularly in certain cluttered scenarios, visual-spatial noise and background redundancy further disrupt attention distribution, significantly degrading the generalization capabilities of existing methods in unseen environments. To address these issues, this paper proposes the Secondary Realignment (SR) framework. It decouples vision-language alignment and vision-action alignment into two stages, mitigating More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079694 - 08 May 2026
Abstract Cyberattacks have increased in frequency and complexity in recent years, resulting in significant consequences for organizations. The negative consequences of cyberattacks force organizations to implement adequate cybersecurity measures to prevent and mitigate the impact of these attacks. Analysis of network traffic is essential for determining whether a cyberattack has been conducted. Intrusion detection systems (IDS) are used to detect malicious actions or irregularities in information systems. In conjunction with artificial intelligence (AI), they enable the development of intelligent intrusion detection systems. This paper presents an intelligent method of network traffic classification for securing systems with… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079941 - 08 May 2026
(This article belongs to the Special Issue: Cyber Attack Detection in Cyber-Physical Systems)
Abstract Advanced Persistent Threats (APTs) are stealthy cyberattacks that can evade detection in system-level audit logs. Provenance graphs encode these logs as interacting entities and events, exposing a causal and dependency structure that is often obscured in linear representations. Prior provenance-based detectors typically apply anomaly detection over such graphs, yet they frequently incur high false-positive rates and produce coarse grained alerts; moreover, approaches that heavily depend on node-specific identifiers (e.g., file paths) can learn spurious correlations, reducing robustness and limiting reliability across heterogeneous workloads. In this paper, we present Self-Training Adaptive Graph Encoder
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.081953 - 08 May 2026
Abstract The rapid emergence of sophisticated, dynamic, and rare or previously unseen attack pattern exposes fundamental limitations of conventional intrusion detection systems (IDS) based on static learning architectures. While deep learning (DL) models have demonstrated strong performance by capturing complex spatial and temporal traffic patterns, existing DL-based IDS largely rely on fixed decision structures, restricting adaptability to evolving threats. Furthermore, current hybrid DL-metaheuristic approaches typically use such metaheuristics as offline or auxiliary optimizers, without interacting with the deep model’s internal latent representations. This paper introduces a novel co-evolutionary IDS that establishes a tight, bidirectional coupling between… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079895 - 08 May 2026
(This article belongs to the Special Issue: Intelligent Perception, Decision-making and Security Control for Unmanned Systems in Complex Environments)
Abstract Path planning for unmanned systems in complex environments must simultaneously satisfy safety, kinematic feasibility, and real-time performance requirements. Monte Carlo Tree Search (MCTS) offers advantages such as model-free operation, strong interpretability, and anytime planning capability, but it suffers from large branching factors, excessive search depths, and poor convergence under sparse reward conditions in high-dimensional state spaces. To address these challenges, this paper proposes a Heuristic Rolling Monte Carlo Tree Search (HRMCTS) framework. First, the path planning problem is formulated as a constrained Markov decision process, where the state consists of position and heading, and actions… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.077825 - 08 May 2026
Abstract This article presents a particular tree covering technique. To cover a set of nodes belonging to an unknown tree, a set of connected small Steiner trees is proposed. These Steiner trees can be represented as hyperedges, and a chain or tree of hyperedges provides the cover. The model allows the calculation of approximate (partial) spanning trees in graphs. The idea of covering a set of nodes by hyperedges can be used directly in Steiner heuristics. The NP-hard Steiner problem in graphs is one of the most studied graph-related problems. Several heuristics are known to give More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080767 - 08 May 2026
Abstract Accurate grasp detection is fundamental to successful robotic manipulation. Existing methods achieve reliable performance under good light conditions. However, their performance in low-light environments suffers from severe degradation due to the diminishing discriminative ability of visual features. In this paper, a novel low-light aware hybrid network LAH-Net is proposed. It comprises an alternating transformer-CNN module (ATCM) between the encoder and decoder, and a knowledge distillation-guided low-light enhancement module (KDLEM) before the encoder, which is activated by an illumination gate under low-light conditions. To generate highly robust and synergistic features, the ATCM module facilitates the iterative… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.078762 - 08 May 2026
Abstract In semiconductor packaging processes, the wire bonding procedure, which connects chips to substrate lead frames using metal wires, is a crucial step. The quality of the bonding joints significantly affects product performance, including signal integrity and reliability, and is challenging to verify after subsequent processes. To mitigate the risk of defective bonding joints entering the assembly packaging stages of production, this study integrates the concepts of Fault Detection and Classification (FDC) and machine learning into the wire bonding process for enhanced anomaly detection. Production data from the machines were collected and analyzed using statistical methods More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.079056 - 08 May 2026
Abstract Road-surface identification is important for transportation monitoring and maintenance. However, this task is challenging due to the complexity of vibration signals, feature overlap among different surface types, and variations in real-world operating conditions. These challenges become more significant in time-series classification, where models must achieve high accuracy while remaining computationally efficient and suitable for low-cost hardware. This study investigates the design and evaluation of an automatic road-surface classification system using motion data collected from inertial sensors mounted on a vehicle, including accelerometers and gyroscopes. The system segments synchronized IMU signals into fixed-length windows and assigns… More >
 Open Access
Open Access
ARTICLE
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.080444 - 08 May 2026
Abstract Recent advancements in AI-synthesized speech have resulted in highly realistic deepfake audio, posing severe threats to authentication systems and digital media trust. Existing detection models struggle to generalize across diverse synthesis methods, especially those involving neural codec-based Audio Language Models (ALMs). In this work, we propose UniTector++, a novel prosody-aware, multi-stream detection architecture that generalizes across vocoder- and codec-based synthesis. UniTector++ incorporates three complementary streams—Whisper-based semantic embeddings, high-level prosodic features, and codec artifact representations—fused through a Multi-Domain Adaptive Graph Attention Fusion (MAGAF) module. Furthermore, an Emotion-Consistency Verification Module (ECVM) reinforces alignment between speech style and More >
 Open Access
Open Access
EDITORIAL
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.081439 - 08 May 2026
(This article belongs to the Special Issue: Advanced Computational Modeling and Simulations for Engineering Structures and Multifunctional Materials: Bridging Theory and Practice)
Abstract This article has no abstract. More >
 Open Access
Open Access
REVIEW
CMC-Computers, Materials & Continua, Vol.88, No.1, 2026, DOI:10.32604/cmc.2026.070014 - 08 May 2026
Abstract This research paper explores how wireless communication has played a key role in transforming healthcare and bringing in a new era of personalized, linked, and data-driven medical services. With the proliferation of wireless healthcare applications, ensuring the security and privacy of sensitive medical data has become paramount. We discuss the potential of blockchain technology, to address challenges and to secure next-generation wireless healthcare. We have elaborated how blockchain’s core characteristics, such as immutability and decentralization, can create a secure and transparent environment for sharing and storing medical data. Additionally, this paper examines how emerging technologies,… More >