DOI:10.32604/cmc.2022.019866
| Computers, Materials & Continua DOI:10.32604/cmc.2022.019866 | 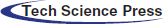 |
| Article |
A Robust Video Watermarking Scheme with Squirrel Search Algorithm
1Computer Science and Engineering, Lovely Professional University, Punjab, 144411, India
2Department of Management Information Systems, King Khalid University, Guraiger, Abha, 62529, Saudi Arabia
3Department of Civil Engineering, College of Engineering, Taif University, Taif, 21944, Saudi Arabia
*Corresponding Author: Aman Singh. Email: amansingh.x@gmail.com
Received: 29 April 2021; Accepted: 19 July 2021
Abstract: Advancement in multimedia technology has resulted in protection against distortion, modification, and piracy. For implementing such protection, we have an existing technique called watermarking but obtaining desired distortion level with sufficient robustness is a challenging task for watermarking in multimedia applications. In the paper, we proposed a smart technique for video watermarking associating meta-heuristic algorithms along with an embedding method to gain an optimized efficiency. The main aim of the optimization algorithm is to obtain solutions with maximum robustness, and which should not exceed the set threshold of quality. To represent the accuracy of the proposed scheme, we employ a popular video watermarking technique (DCT domain) having frame selection and embedding method for watermarking. A squirrel search algorithm is chosen as a meta-heuristic algorithm that utilizes the stated fitness function. The results indicate that quality constraint is fulfilled, and the proposed technique gives improved robustness against different attacks with several quality thresholds. The proposed technique could be practically implemented in several multimedia applications such as the films industry, medical imagery, OOT platforms, etc.
Keywords: Meta-heuristic algorithm; constrain optimization problem; fitness fiction; frame selection; squirrel search algorithm
As the growth of internet prevailing multimedia usage is easy to be shared and accessed, editing tools and software are so readily available that their utilization is inevitable up to such an extent that no professional knowledge is required to manipulate digital multimedia. To protect the digital data in a shared medium from illegal manipulation, there is a need for a unique and popular technique known as digital watermarking. Digital watermarking is a process to embed an imperceptible watermark into a host/cover digital content in such a way that the spread of watermark bits is scattered in the host evenly. Also, it must be infeasible to alter the watermark bits and could be extracted through some computation. The main applications of digital watermarking are copyright protection, ownership identification [1]. Some of the other applications include broadcast monitoring, modification detection, authentication, and source tracking, etc reflected in Fig. 1a. This paper discusses video watermarking, which proposes authentication to the video by embedding watermark data into the cover video. There are many challenges in video watermarking. One of the major challenges is a design scheme that provides robustness to the watermarking and loss of quality is a challenge that is reflected in Fig. 1b. Whereas robustness is the tendency of the watermark to not getting destroyed during an attack makes it fault-tolerant. The significance of one is often highlighted over the other, as per the need for required quality in the application [2]. There is a tradeoff between imperceptibility (quality) and robustness (fault-tolerance) i.e., if one is required the second must be compromised. Imperceptibility significantly affects the visual quality of the video.
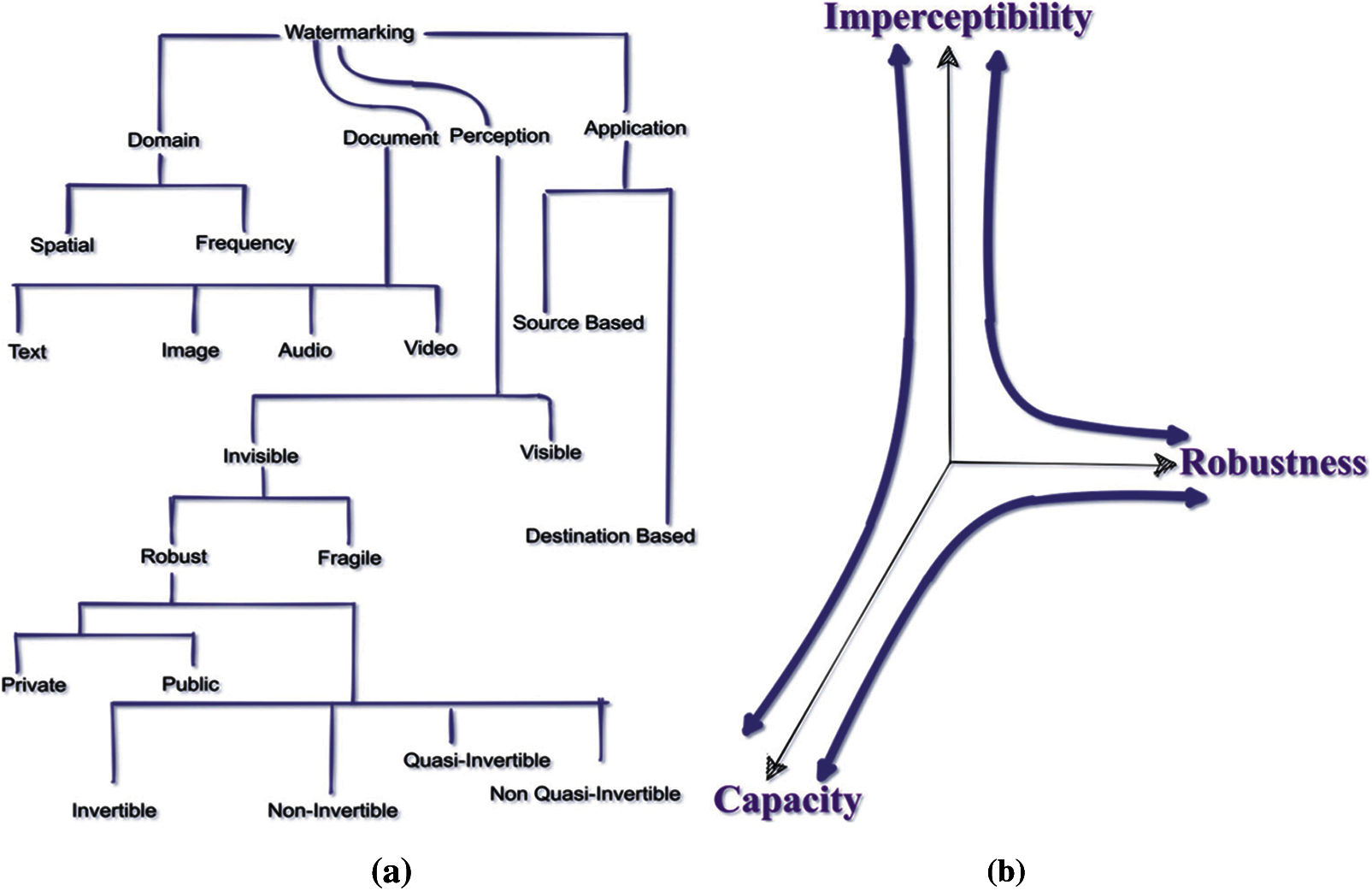
Figure 1: (a) Watermarking techniques (b) Relationship among watermark capacity, imperceptibility, and robustness
Meanwhile, the minimal modification would result in reduced robustness of the algorithm [3]. To have the balance between the three concepts, we employ a meta-heuristic optimization algorithm (SSA (Squirrel Search Algorithm)). These computed objective functions are then utilized to rank the solutions and find the optimal results. This will generate robust watermarking schemes with distortions below the sensitivity threshold [4].
Knowledge embedding in multimedia data is a field that has lately gotten a lot of attention [5]. The Major contribution of the paper is integrated into the following points.
(a) We have proposed the frame selection technique to chose optimal frames.
(b) We have proposed a novel technique for embedding a watermark that is based on DCT domain block-based conversion along with an optimization algorithm.
(c) We have proposed the calculation of efficiency and performance of the presented scheme against several image processing attacks.
Kavitha Soppari et al. have done more research studies in implementing robust watermarking through clustering techniques as most of the transform-domain watermarking approaches were build on Discrete Cosine Transform (DCT). This is because it is robust to JPEG lossy compression. Therefore, the author proposes an efficient digital watermarking mechanism based on an optimized clustering method. Mohammad Moosazadeh et al. proposed an embedding method that depends upon the relationships in between DCT coefficients. The watermarking parameters are optimally selected using a rarely used optimization algorithm of watermark embedding known as Teaching-learning-Based Optimization (TLBO). Vipul and Roohie stated the considerable time complexity of meta-heuristic search algorithms is not applicable for time-sensitive applications. For this, they utilize the DCT domain for embedding watermark followed by nature-based optimization algorithm ant colony optimization to search optimal parameters. Assem Mahmoud Abdelhakim et al. provided a smart scheme for watermarking by incorporating a meta-heuristic search technique known as Artificial Bee Colony along with an embedding function to achieve an optimized functionality. The quality of watermarking is insured by constraint optimization.
Squirrel Search Algorithm
There is no single nature-based optimization strategy that can solve all optimization problems in the best possible way. This means that an optimization algorithm is good at solving a certain set of problems but not so well at solving others. As a result, a new unconstrained numerical optimization algorithm called Squirrel Search is proposed. The foraging of flying squirrels can be divided into two scenarios [6].
(i) Assumptions in SSA
In a deciduous forest, there are n flying squirrels, and each squirrel is thought to be on one tree. Each flying squirrel uses a complex foraging behavior to hunt for food and make the best use of the available resources. There are only three types of trees in the forest: I Regular tree (ii) Oaktree (acorns) (abundant food source) hickory tree (iii) (alternate food source).
(ii) Implementation of SSA
The game begins with a random location of a flying squirrel (FS). In a d-dimensional search space, the location of FS is represented by a vector. The random initialization of ‘n’ number of FS in the forest and each vector specifies the direction of the ith FS. A matrix FS can be used to represent the location of all FS and shown by below equation
The jth dimension of ith squirrel is defined by FSi,j equation
This provides a uniform allocation for allocating the initial position of each FS in the Forest.
FSL: Lower Bound of FSi
FSU: Upper Bound of FSi
U (0, 1): random no. between [0,1]
(iii) Fitness Evaluation
In the user's fitness function, the value of the decision variable (solution vector) and its related value is stored in ‘f’. Some of the constants considered are dg:random gliding distance, R1: random no. [0,1], t: current iteration tree Gc: Constant to achieve balance b/w exploration and exploitation, dg: (hg/tan(Q)) hg: loss in height after gliding, Q: arctan(D/L), D: drag force produced, L: Sum of lift at equilibrium, L = 1/(2ÞCL V2S), Þ: 1.204 kgm3 (air density), CL = Lift Coefficient in the range of [0.675, 1.5], V = 5.25 m/sec (speed of flying squirrel (avg)), S = 154 cm2 (Surface area), D = 1/(2ÞCDV2S), CD: Drag Coefficient (0.60) [6] as mentioned in Eq. (3).
Case 1: FS on Acorn tree (FSat) moving towards hickory tree (FSht). Location is updated as given in the following given Eq. (4).
where R1 is a random number between [0, 1]
Case 2: FS on a normal tree (FSnt) moving towards acorn tree (FSat) location is updated as given in following given Eq. (5).
where R2 is a random number between [0, 1]
Case 3: FS on a normal tree (FSnt) and already passed acorn tree and now moving towards hickory tree (FSht), Location is updated asgiven in following given Eq. (6).
where R3 is a random number between [0, 1]
(iv) Seasonal Monitoring Condition
Since foraging in the winter was more expensive and dangerous, FS became less successful than in the autumn. Incorporating such behavior results in a more practical strategy that avoids being stuck in a locally optimal solution. Per iteration, calculate the seasonal constant (Sc) Eq. (7) [6].
where t = 1, 2, 3 iterations
Check Sct < Smin where Smin is the minimum value of Seasonal Constant Computed as Eq. (8) [6].
t < current iteration tm < max iteration
If the condition is true, then randomly reallocating FS did not explore the forest by following Eq. (9) [6].
where Levy is random walk-through Levy distribution.
The discrete cosine transform is then applied to the blocks of a grayscale image used as the carrier image, and the DCT coefficients are quantized using the quantization table represented in the JPEG norms, which is used where an image requires a very high compression rate [7].
Optimization problem to search for the optimum embedding strength parameter (k and p) for embedding watermark problem formulated in Eq. (10).
It assigns a score to each solution based on how effective it is at solving the problem. Sorting, declaring, and selecting at random: The following three minimum sorted fitness values are known to have (normal food source), and they are progressing towards (optimal food source). The rest of the tree is regular. The rest FS fitness value is used to make a random pick, which means aiming towards the best food source. The proposed fitness function Algorithm 1 in pseudo-code is followed by a flow diagram given in Fig. 2.

The robustness of the proposed method against various kinds of attacks such as median filtering, Gaussian noise [8], Sharpening, Rotation attack. According to the watermark experiment findings, the suggested scheme performs satisfactorily in terms of image distortion and embedded watermark retrieval, even after the original image has been damaged by several assaults [9]. This approach can effectively avoid rotating attacks, and only half of the points need to be scanned [10]. Spatial scanning, duplication, cropping, scaling, translation, compression, and rotating are examples of attacks that may be carried out deliberately or accidentally [11]. We checked the watermarking algorithm's resiliency against a series of four different attacks for various videos and enhanced the decoding BER (bit error rate) [12]. When constructing an appropriate architecture, we have a list of typical attacks or threats to remember. PSNR (peak signal-to-noise ratio), MSE (mean squared error), and NCC (normalized cross-correlation) are a few of the output metrics described briefly [13].
Figure 2: Fitness function algorithm flow diagram [14]
Divide the host image I, of the size P × Q, into 8 × 8 blocks. Transform each image block I p, q and its adjacent block I p+1, q into DCT coefficients as given in Eq. (11), and also we have given Algorithm 2 to represent in the form of pseudo-code.
Adjust the value of two coefficients according to the watermark bit Wp,q, which is the bit location at the pth row & qth column of the watermark image. As shown in Eq. (12) below.
This scaling parameter is calculated by associating the imperceptibility quality of each watermark with the imperceptibility quality of the host image to mitigate the tradeoff between robustness and imperceptibility [15]. α ← Ensure absolute difference between modified coefficients large enough to provide the required robustness. β ← Ensures how much proportion of the value α can be used in a coefficient adjustment. As shown in Eq. (13) below.

4 Intelligence Evolutionary Algorithm
With the rapid development of modern technology, the complex evolutionary problems are too difficult to be answered by conventional optimization algorithms. This challenge can be dealt with by incorporating an evolutionary intelligence algorithm. The implementation is done by embedding a watermark in the DCT domain, accompanied by a nature-based optimization watermark [16]. This is due to the resistance to lossy JPEG compression [17]. Attacks like frame lowering, averaging, cropping, and median filtering, as well as unintended attacks like noise and compression, can breach copyright information in a video [18]. The evolutionary intelligence algorithms can be divided into 3 categories as given below.
4.1 Evolutionary Heuristic Algorithms
The Evolutionary heuristic algorithms are inspired by biological evolution like reproduction, mutation, recombination, and selection. It plays a vital role in estimating accurate solutions or optimal solutions from a population of solutions. Moreover, it solves difficult problems by using a fitness function which is using the evolutionary algorithm as a tool for problem-solving also known as Evolutionary Computation (EC). Genetic Programming (GP): It is an extension of GA used for testing and selecting the best choices among the set of results [19]. And by integrating the MPEG specifications with the classic block-adaptive-video watermarking systems, can get better results [20].
4.2 Physics Heuristic Algorithms
These are originated by physical phenomena, which are then conceptually applied to obtain optimal solutions. After melting the energy is exceedingly high and the temperature slowly drops to a stable solid-state having minimum energy (optimal solution). Similarly, Gravitational, The magnetic optimization.
4.3 Nature Heuristic Algorithms
These are inspired by biological practices and phenomena in nature. There are several algorithms in this class such as Ant Colony Optimization that are based on naturally excrete pheromones in their path which act as an indicator better path. Another such algorithm is the particle swarm optimization algorithm, which is based on bird's practices in seeking food. Similarly, Artificial Bee Colony is based on the adaptation of the foraging practices of the honeybee. The bee's population is formed through 3 types of bees based on their work. Mainly Employee bee, onlooker bee and scout bee.
We looked at a variety of image matching methods before settling on the histogram process. Histogram-based methods are ideal for determining the total changes in an image. An image's color histogram can be calculated by dividing a color space, such as RGB. The distinction between two pictures dependent on color histograms H1 and H2 can be calculated as in Eq. (14). Fig. 3 depicts the frame selection flow diagram to more clearly explain the algorithm. Algorithm 3 is also stated for the reader's reference.

It significantly affects the visual quality of the video. So, to ensure the quality of the video watermarking, we need to calculate a measure that can indicate the level of imperceptibility. It is calculated through a mathematical ratio known as Peak Signal to Noise ratio (PSNR) as per Eqs. (15)–(16). The term robustness refers to the embedded watermark's ability to withstand image manipulation and geometric attacks.
fk→ original video frame fkw →Watermarked video frame
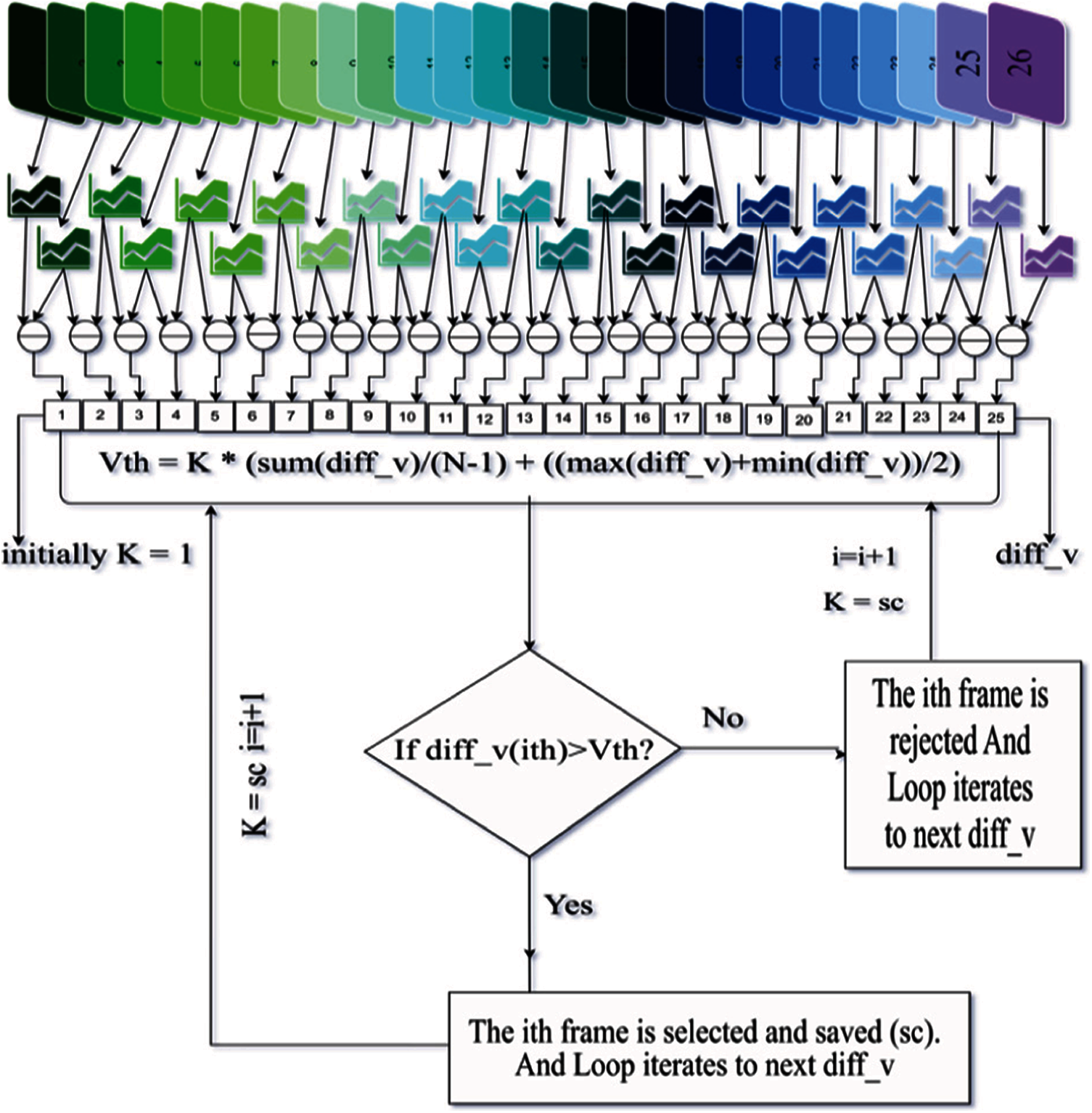
Figure 3: Frame selection algorithm flow
Robustness is vital for granting capability to withstand different image processing and geometric attacks and the quality of digital content must not be degraded. Related attacks include smoothing, sharpening, compression, de-noising, filtering, scaling, cropping, and rotation. The robustness of watermarking algorithms is usually measured using normalized correlation (NC) and bit error rate (BER). NC is used to calculate the degree of resemblance between the derived and initial watermarks. It can be calculated through a mathematical measure known as Normalize Correlation that ranges between 0 to 1 [21]. A higher value of NC stronger the anti-attack ability, as given in Eq. (17).
The results were evaluated in MATLAB 2014a using an i5 processor. The frame selection time and embedding time is dependent on the processing power of the processor and the size of the RAM. The observed results are based on the watermark embedding time, frame selection time, and optimization algorithm time. For testing the algorithm, a total of 5 CIF (Common Interchange Format) videos are utilized, and the frame selection technique used is based on scene change in the video. Fig. 4 shows the test videos list with the chosen frames from each video. The higher value the PSNR value indicates the proposed technique will have a minimum loss in quality of output. Similarly, for greater the value of NC, more resistance against attacks. The testing is started with converting videos in mp4 format followed by frame extraction. The frames extracted are in the PNG format to withstand quality loss. The selected frames are then embedded through embedding algorithms with hyperparameters values obtained through optimization algorithm. Finally, we bring the efficiency of the proposed work by applying several image processing attacks and then calculating NC values [22]. Tabs. 1–3 represents number of frames selected, quality metrics values and a comparison analysis of existing frame selection techniques.

Figure 4: Selected frames from videos: (a) Akiyo #251(252), (b) Bus #126(127), (c) Football #74(218), (d) News #77(252), (e) Container #251(252), (f) Watermark



Experimental Tests for Time Complexity: Tab. 4 describes the processing time (in seconds) associated with the frame selection and embedding algorithm applied to the test videos. The duration is entirely based on hardware processing power. Also, it depends upon the number of selected frames and the total number of frames in the video. For football and news number of frames selected is 2 out of 218 and 252 frames respectively. The average frame selection time is nearly the same. Moreover, the total number of frames in the video also lead to an increase in the execution time due to which we can see the football video having 2 frames out of 252 frames have slightly higher embedding time (3.1747) to the Akiyo video having 252 frames and 1 frame selected (3.164). Figs. 5, 6 signify plots drawn against quality metrics and frame selection time, embedding time Figs. 7–10 signify plots drawn against gaussian noise, sharpening attack, rotation, median filtering attacks.


Figure 5: Plot of PSNR, NC, K, BER w.r.t the videos taken in the proposed work for watermark against no attack. (a) Average PSNR, (b) Average NC, (c) Average BER

Figure 6: Plot of total frame selection time and total embedding time (in seconds) for 5 videos. (a) Total frame selection time (in seconds). (b) Total embedding time (in seconds)

Figure 7: Plot of PSNR, NC, P, BER w.r.t the videos taken in the proposed work for watermark against Gaussian attack. (a) Average PSNR, (b) Average NC, (c) Average BER
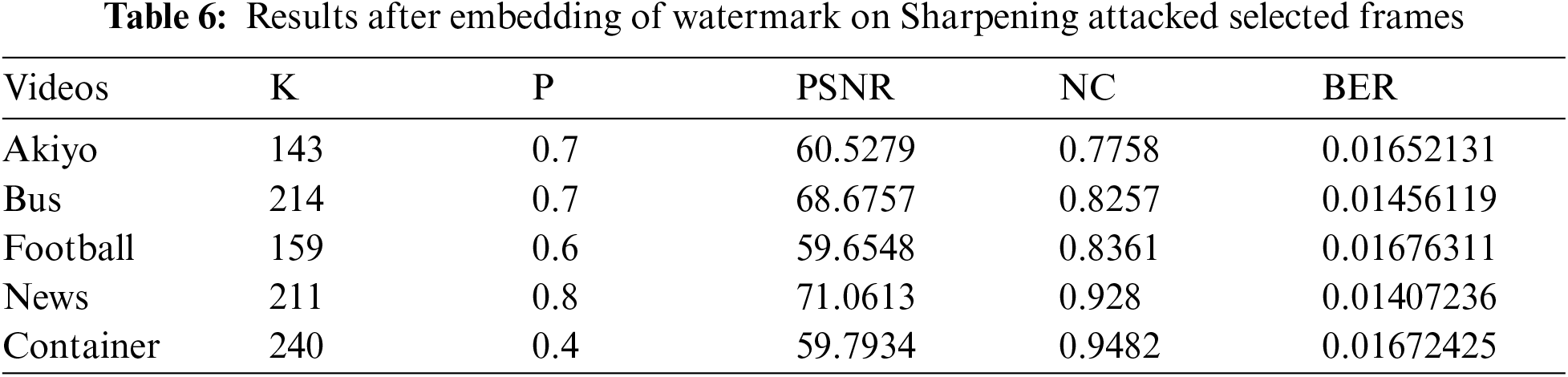
The fault tolerance of the proposed technique is tested against several attack scenarios like Gaussian Noise in Tab. 5, Sharpening in Tab. 6, Median filtering attack in Tab. 7, and Rotation attack in Tab. 8. To account for the lost number of attacks on every watermarked frame to measure the quality of the proposed technique [22]. The second attack on the selected frames will stretch the pixel distribution in the image and highlights the fine image details [22].

Figure 8: Plot of PSNR, NC, K, BER w.r.t the videos taken in the proposed work for watermark against Sharpening attacked. (a) Average PSNR, (b) Average NC, (c) Average BER

Figure 9: Plot of PSNR, NC, BER w.r.t the videos taken in the proposed work for watermark against Rotation attack. (a) Average PSNR, (b) Average NC, (c) Average BER

Figure 10: Plot of PSNR, NC, BER w.r.t the videos taken in the proposed work for watermark against median filter attacked. (a) Average PSNR, (b) Average NC, (c) Average BER



We proposed a unique block-based embedding technique to entertain quality loss in watermarking process. For efficient time and space complexity, we utilize frame selection for the application of watermark embedding, which will be a time-consuming and space-expensive method. This frame selection is based on the number of scenes that change in a particular test video. This is followed by block-based application of DCT2 and searching for optimal parameters for embedding based on black and white watermark bits. The approach is tested against several image processing attacks such as Gaussian Noise, Image Sharpening, Rotation attack, Median filter attack, etc. The results indicate good levels of robustness against many attacks. Further security can be added in future work such as watermark encryption and more suitable frame selection for videos having no detectable scene change.
Acknowledgement: The authors would like to express their gratitude to King Khalid University, Saudi Arabia for providing administrative and technical support. This work was supported by the Deanship of Scientific Research, King Khalid University, under Grant GRP/358/42 and would also like to thank Taif University Researchers Support Project Number (TURSP-2020/196) Taif University, Taif, Saudi Arabia.
Funding Statement: The authors would like to express their gratitude to King Khalid University, Saudi Arabia for providing administrative and technical support. This work was supported by the Deanship of Scientific Research, King Khalid University, under Grant GRP/358/42 and the study was also funded by Taif University Researchers Support Project Number (TURSP-2020/196) Taif University, Taif, Saudi Arabia.
Conflicts of Interest: The authors declare that they have no conflicts of interest to report regarding the present study.
1. A. M. Abdelhakim, H. I. Saleh and A. M. Nassar, “A quality guaranteed robust image watermarking optimization with artificial bee colony,” Expert Systems with Applications, vol. 72, pp. 1–10, 2016. [Google Scholar]
2. L. Agilandeeswari and K. Ganesan, “A robust color video watermarking scheme based on hybrid embedding techniques,” Multimedia Tools and Applications, vol. 75, pp. 8745–8780, 2016. [Google Scholar]
3. D. Bhowmik, M. Oakes and C. Abhayaratne, “Visual attention-based image watermarking,” Institute of Electrical and Electronics Engineers Access, vol. 2016, pp. 1–17, 2016. [Google Scholar]
4. A. Cedillo-Hernandez, M. Cedillo-Hernandez, M. N. Miyatake and H. P. Meana, “A spatiotemporal saliency-modulated JND profile applied to video watermarking,” Journal of Visual Communication and Image Representation, vol. 52, no. 18, pp. 106–117, 2018. [Google Scholar]
5. F. Hartung and B. Girod, “Digital watermarking of Raw and compressed video,” in Proc. of the Digital Compression Technologies and Systems for Video Communications, Milan, vol.1996, pp. 205–213, 1996. [Google Scholar]
6. M. Jain, V. Singh and A. Rani, “A novel nature-inspired algorithm for optimization: Squirrel search algorithm,” Swarm and Evolutionary Computation, vol. 2019, no. 49, pp. 148–175, 2019. [Google Scholar]
7. L. Guang-Qi, Z. Xiao-Shi, Z. Yan-Ling and L. Na, “A robust digital video watermark algorithm based on DCT domain,” in Proc of the Int. Conf. on Computer Application and System Modeling, Taiyuan, vol. 2010, pp. 1–26, 2010. [Google Scholar]
8. M. Masoumi and S. Amiri, “A blind scene-based watermarking for video copyright protection,” AEU-International Journal of Electronics and Communications, vol. 67, no. 6, pp. 528–535, 2013. [Google Scholar]
9. M. Moosazadeh and G. Ekbatanifard, “A new DCT-based robust image watermarking method using teaching-learning-based optimization,” Journal of Information Security and Applications, vol. 47, pp. 28–38, 2019. [Google Scholar]
10. W. Pei, Z. Zheng and J. Ying, “Novel video watermark technique in motion vectors,” Institute of Electrical and Electronics Engineers Access, vol. 2008, no. 8, pp. 1–23, 2008. [Google Scholar]
11. Poonam and S. M. Arora, “DWT-SVd based robust digital watermarking for digital image,” Procedia Computer Science, vol. 132, pp. 1441–1448, 2018. [Google Scholar]
12. R. O. Preda and D. N. Vizireanu, “A robust digital watermarking scheme for video copyright protection in the wavelet domain,” Measurement, vol. 43, pp. 1720–1726, 2010. [Google Scholar]
13. H. Sahu and E. Patil, “A review on digital video watermarking,” International Research Journal of Engineering and Technology, vol. 7, no. 5, pp. 5432–5436, 2020. [Google Scholar]
14. C. Sharma and A. Bhaskar, “A review on video watermarking techniques for compressed domain with optimization algorithms,” Materials Today: Proceedings, vol. 2020, pp. 1–9, 2020. [Google Scholar]
15. S. Sharma, H. Sharma and J. B. Sharma, “An adaptive color image watermarking using RDWT-SVD and artificial bee colony-based quality metric strength factor optimization,” Applied Soft Computing Journal, vol. 84, pp. 1–18, 2019. [Google Scholar]
16. V. Sharma and R. N. Mir, “An enhanced time efficient technique for image watermarking using ant colony optimization and light gradient boosting algorithm,” Journal of King Saud University, vol. 2019, pp. 1–12, 2019. [Google Scholar]
17. K. S. Soppari and N. S. Chandra, “Development of improved whale optimization-based FCM clustering for image watermarking,” Computer Science Review, vol. 37, pp. 1–21, 2020. [Google Scholar]
18. P. S. Venugopala, H. Sarojadevi, N. N. Chiplunkar and V. Bhat, “Video watermarking by adjusting the pixel values and using scene change detection,” in Proc 2014 Fifth Int. Conf. on Signal and Image Processing, Bangalore, vol. 13, pp. 259–264, 2013. [Google Scholar]
19. Y. Wang and T. Du, “An improved squirrel search algorithm for global function optimization,” Algorithms, vol. 80, no. 12, pp. 1–29, 2019. [Google Scholar]
20. D. Ye, C. Zou, Y. Dai and Z. Wang, “A new adaptive watermarking for real-time MPEG videos,” Applied Mathematics and Computation, vol. 185, no. 2, pp. 907–918, 2007. [Google Scholar]
21. X. Yu, C. Wang and X. Zhou, “A review on robust video watermark algorithms for copyright protection,” Applied Science, vol. 8, no. 10, pp. 1–26, 2018. [Google Scholar]
22. C. Sharma, A. Bagga, R. Sobti, T. R. Lohani and M. Shabaz, “A secured frame selection based video watermarking technique to address quality loss of data: Combining graph based transform, singular valued decomposition, and hyperchaotic encryption,” Security and Communication Networks, vol. 2021, no. 5536170, pp. 1–19, 2021. [Google Scholar]
 | This work is licensed under a Creative Commons Attribution 4.0 International License, which permits unrestricted use, distribution, and reproduction in any medium, provided the original work is properly cited. |